
Ransomware, like no other threat, puts fear into the hearts and minds of data administrators. From small businesses to hospitals and critical infrastructure, organizations of all sizes have been victims of ransomware in recent years. Sadly, ransomware protection is more a buzzword than a single product or solution.
The cybersecurity vendors doing the most for clients in addressing ransomware are a list of familiar and emerging security tools and software for malware detection and response. Beyond next-generation antivirus, backup, and recovery features, increasing protection across the security architecture is essential to combating ransomware.
Read on to learn more about ransomware protection, the best vendors on the market, how products compare, and what to consider when evaluating solutions.
Comparing the Best Ransomware Protection
| Vendor | Cloud | On-Premises | Backup | Disaster Recovery | Email Security | DLP | Patch Mgmt | Firewall | Sandbox | Windows | Linux |
| Acronis | ✅ | ✅ | ✅ | ✅ | ✅ | ✅ | ✅ | 🚫 | ✅ | ✅ | ✅ |
| Avast | ✅ | ✅ | ✅ | ✅ | ✅ | ✅ | ✅ | ✅ | ✅ | ✅ | ✅ |
| AVG | ✅ | ✅ | ✅ | 🚫 | ✅ | ✅ | ✅ | ✅ | 🚫 | ✅ | ✅ |
| Bitdefender | ✅ | ✅ | ✅ | ✅ | ✅ | 🚫 | ✅ | ✅ | ✅ | ✅ | ✅ |
| Check Point | ✅ | ✅ | ✅ | ✅ | ✅ | ✅ | ✅ | ✅ | ✅ | ✅ | ✅ |
| ESET | ✅ | ✅ | ✅ | ✅ | ✅ | ✅ | ✅ | ✅ | ✅ | ✅ | ✅ |
| Kaspersky | ✅ | ✅ | ✅ | ✅ | ✅ | ✅ | ✅ | ✅ | ✅ | ✅ | ✅ |
| Malwarebytes | ✅ | ✅ | ✅ | ✅ | 🚫 | 🚫 | ✅ | 🚫 | ✅ | ✅ | ✅ |
| Sophos | ✅ | ✅ | ✅ | ✅ | ✅ | ✅ | ✅ | ✅ | ✅ | ✅ | ✅ |
| Trend Micro | ✅ | ✅ | ✅ | ✅ | ✅ | ✅ | ✅ | ✅ | ✅ | ✅ | ✅ |
Best Ransomware Protection Tools

Acronis
Acronis offers cybersecurity solutions to service providers, businesses, and individuals, bolstering their security posture and guarding against ransomware.
Acronis Cyber Protect includes advanced security features like exploit prevention, URL filtering, and anti-malware to extend protection to web browsing, the recovery process, and backed-up data. Components included in Acronis’ stack solution include data loss prevention (DLP), email security, disaster recovery, and backups.
Acronis Cyber Protect Features
- Built-in backup and recovery for Microsoft Exchange and SQL Servers, and Oracle
- A #CyberFit Score to assess security gaps and offer remediation guidance
- Multi-tenant management like test failover, firewall management, and immutable storage
- Centralized protection plans for managing security configurations across endpoints
- Disaster recovery orchestration supporting Windows and Linux servers, and VMs
Acronis Pros and Cons
Pros
- Ease of use
- 30-day free trial
- Multiple backup options
Cons
- No firewall included
- Disruptive error messages on occasion
- GUI could be more intuitive

Avast
Avast is an antivirus and internet security vendor offering protection solutions for home offices, small businesses, and channel partners like managed service providers (MSP). For up to 100 devices, Avast’s business subscriptions include an online management platform, device malware protection, and IT support via call, email, or webchat. Avast’s additional security products include advanced remote control, antivirus for Linux, and patch management.
Avast Features
- Automated patch management to resolve third-party software vulnerabilities
- Protection for browser-stored passwords susceptible to web attacks
- Comprehensive real-time endpoint protection for Linux distributions
- Webcam protection to prevent malware from accessing web cameras without consent
- Support for Windows, Linux, and macOS infrastructure
Avast Pros and Cons
Pros
- Lightweight and discreet software
- Speed of detecting threats
- 30-day money-back guarantee
Cons
- Installation can be time consuming
- More expensive than alternatives
- Previously collected user data (2020 leak)
AVG
AVG is another antivirus company specializing in malware protection across operating systems and business products for file servers, email servers, patch management, and internet security. Ideal for small businesses, the AVG Antivirus subscriptions offer a cloud console for remote management and protection, dubbed “Shields,” for web traffic, email, files, and suspicious behavior.
The AVG Internet Security Business edition goes a tad farther, offering protection for Microsoft Exchange and password protection for Chrome and Firefox browsers.
AVG Features
- Permanently delete files not to be recovered with the file shredder
- Firewall for blocking potential threats and filtering network traffic
- Scan all links including from social media like Twitter or Facebook
- VPN supporting Windows, macOS, Android, and Apple devices
- Advanced protection for uploads and download to SharePoint servers
AVG Pros and Cons
Pros
- 30-day free trial
- Easy to install and maintain
- Reliable and fast performance
Cons
- No sandbox analyzer
- Premium support is expensive
- Resource intensive with occasional slowdowns

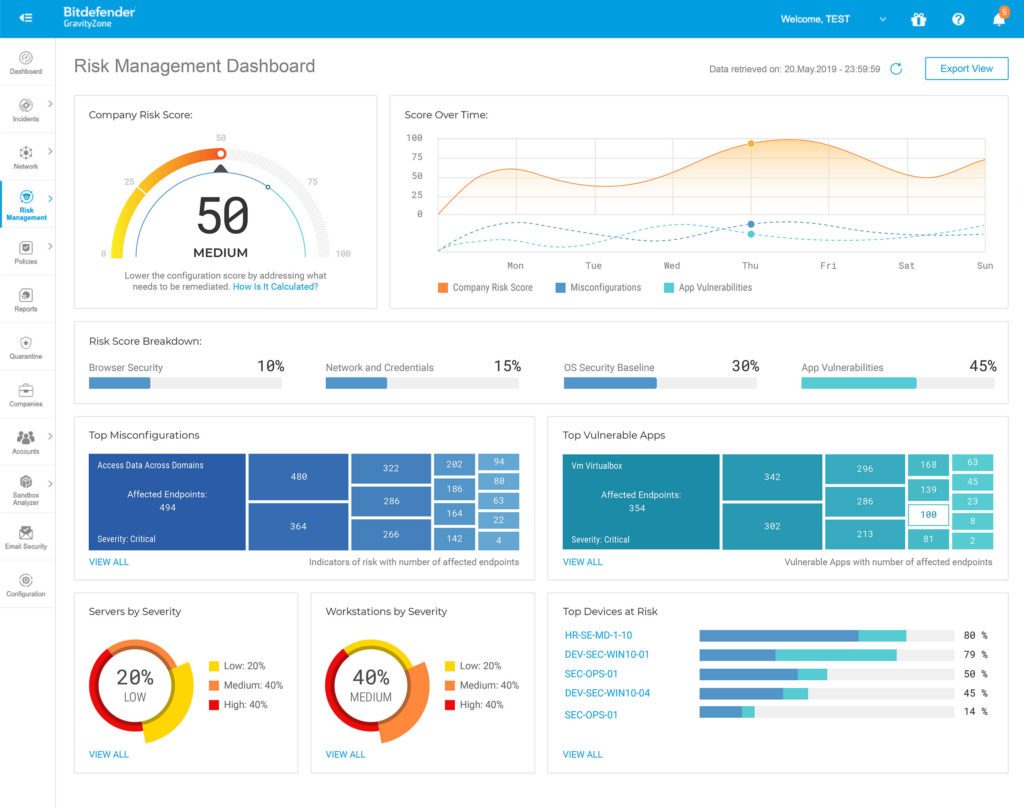
Bitdefender
Bitdefender is an undisputed industry leader for ransomware protection, as the cybersecurity vendor offers a range of tools for endpoint protection and securing servers, containers, email, and mobile devices. Bitdefender’s endpoint detection and response (EDR) capabilities offer customers root cause analysis, incident visualization, and ransomware mitigation through a real-time backup of files before suspicious modifications.
Bitdefender GravityZone has a comprehensive stack of features to protect hybrid endpoints, and add-ons for additional client needs with options for small businesses, medium-to-large businesses, and MSPs.
Bitdefender GravityZone Features
- On-premises and cloud solutions for physical and virtual servers and workstations
- Add-on tools for email security, full disk encryption, and patch management
- Firewall and endpoint risk analytics to control application and device access
- Prevention tools like a sandbox analyzer, machine learning (ML), and anti-exploit
- Managed detection and response (MDR) available as an add-on
Bitdefender Pros and Cons
Pros
- Ease of implementation and integration options
- Comprehensive and scalable endpoint security
- Robust security and anti-ransomware features
Cons
- Reporting could be more granular
- Technical support is hit or miss
- GUI is a bit clunky, causing difficulty navigating
Read more: Top Server Backup Software & Solutions

Check Point
Firewall pioneer Check Point Software Technologies is an end-to-end cybersecurity solutions provider. The company’s unified security solution is Check Point Infinity, made up of Harmony for secure access control, CloudGuard to secure cloud workloads, and Quantum to defend data centers and enterprise network security. Infinity-Vision combines Check Point’s three decades of experience and expertise into a holistic infrastructure protection plan.
Check Point Infinity-Vision Features
- Endpoint protection for phishing, ransomware, and zero-day exploits
- Secure in-browser internet protection to inspect SSL traffic and block malware
- Cloud security for applications like OneDrive, Office 365, Google Workspace, and Teams
- Threat and event management with monitoring, logging, correlation, and reporting
- Extensive suite of network hardware products for on-premises enterprise security
Check Point Pros and Cons
Pros
- 30-day free trial
- Easy to deploy and use
- Comprehensive security controls
Cons
- Resource utilization can be intrusive
- It runs slowly at times
- Lacks support for older Linux operating systems

ESET
ESET is a veteran antivirus and internet security vendor offering malware protection to individuals, businesses, and channel partners. For small to medium companies, ESET PROTECT offers clients on-premises or cloud security management, hybrid endpoint protection, and real-time protection for all data passing through general file servers.
Clients working with various devices and operating systems will benefit from ESET’s support for Windows, macOS, and Linux infrastructure as well as iOS and Android mobile devices.
ESET PROTECT Features
- Threat and endpoint protection with malware scanning, anti-phishing, and spam filtering
- Access to 170+ built-in reports and 1,000 data points for creating custom reports
- Full disk encryption to fully secure entire devices, partitions, and system disks
- Email security blocks all malware and spam at the server level
- Cloud sandbox for isolating and analyzing potential zero-day threats
ESET Pros and Cons
Pros
- 30-day free trial
- Responsive technical support
- Affordable licensing for security value
Cons
- Frequent updates
- User technical expertise required
- Less fit for enterprise security
Kaspersky
Kaspersky is a comprehensive internet security vendor with solutions for individuals, small and medium businesses, and enterprise organizations with over 1,000 employees. From protecting the home office to global data centers, Kaspersky’s stack of cybersecurity products addresses data, endpoint, and network protection.
For enterprise IT environments, the veteran solution provider offers advanced EDR capabilities and additional security products for hybrid cloud workloads, embedded systems, internet gateways, and Microsoft Office 365.
Kaspersky Features
- Standalone solutions for mail servers, network-attached storage, and DDoS protection
- Access to global threat intelligence to remediate and protect against vulnerabilities
- ML-powered behavioral analysis to detect real-time anomalous activity
- Unified endpoint protection deployed on-premises, cloud, or IaaS environment
- Full Office 365 suite protection for Teams, SharePoint, OneDrive, and Exchange
Kaspersky Pros and Cons
Pros
- 30-day free trial
- Extensive security features
- Operating system support for Windows, macOS, and Linux
Cons
- Length of time to complete scans
- Support options could be better
- Impact on device performance and memory utilization
Also read: Best Cloud & Online Backup Services

Malwarebytes
Malwarebytes is an anti-malware software company offering consumers, businesses, and channel partners affordable subscriptions to its next-generation antivirus and endpoint protection solutions.
Ideal for small to medium companies, Malwarebytes’ solution includes a cloud management console, threat isolation, and forensics for Windows and Linux servers. The company’s business solution, Malwarebytes Endpoint Protection, is available for servers and teams up to 100+ devices.
Malwarebytes Endpoint Protection Features
- Behavioral monitoring technology to mitigate zero-day threats like ransomware
- Threat hunting, isolation for sandbox analysis, and disaster recovery
- Linking Engine to trace every installation, modification, process, and executable
- Rollback encrypted, deleted, or modified data up to 72 hours for Windows systems
- Asset management, including on-demand reports, RBAC, SSO, and AD integration
Malwarebytes Pros and Cons
Pros
- 14-day free trial
- Lightweight and easy to deploy
- Multi-layer security and ML-based threat detection
Cons
- Continuous updates can be obtrusive
- Alerts can be misleading or unhelpful
- No built-in email security, firewall, or DLP

Sophos
Sophos is an established network security leader with endpoint protection, managed detection and response, and next-generation firewalls leading its solution stack. Whether it’s on-premises, cloud, or virtual workloads, Intercept X for Servers has advanced features to defend against the latest threats.
As an EDR solution, clients benefit from Sophos advancements in extended detection and response (XDR), orchestrating a comprehensive security system model.
Sophos Intercept X Features
- Cloud security posture management (CSPM) for robust cloud data protection
- AI-powered threat detection for known and unknown, signatureless malware
- Automatic file recovery and behavioral analysis for ransomware protection
- Threat hunting, intelligence, and remediation via Sophos’ expert SOC personnel
- Reporting for administrators on attack and exploit forensic details
Sophos Pros and Cons
Pros
- 30-day free trial
- Scalable and easy to configure
- Strength of threat detection capabilities
Cons
- Resource intensive
- Technical support is hit or miss
- More expensive than alternatives

Trend Micro
Next to Check Point, Trend Micro offers the most comprehensive portfolio of cybersecurity products for individual users up to enterprise networks. Its suite of solutions includes XDR capabilities, zero trust insights, email security, and a handful of tools for securing hybrid cloud infrastructure.
For network defense, Trend Micro’s intrusion prevention system (IPS), global threat intelligence, and advanced threat detection all aid administrators in actively blocking inbound, outbound, and lateral attacks.
Trend Micro Features
- Execute a root cause analysis and develop an attack profile with asset impact
- Cloud-native security integrated with tools from AWS, Azure, GCP, and VMware
- Access to 240+ global templates for data loss prevention
- Open source vulnerability and license management through a partnership with Snyk
- Security solutions for applications, containers, file storage, networks, and workloads
Trend Micro Pros and Cons
Pros
- 30-day free trial
- Feature-rich and scalable
- Responsive technical support
Cons
- Less user-friendly interface
- Lack of support for older clients
- Documentation hard to navigate
Read more: Best Server Virtualization Software
Ransomware Protection Solutions: Honorable Mentions
What Is Ransomware?
Ransomware is an advanced malware strain where a threat actor encrypts entire segments of an IT environment and holds data hostage at an often steep price. Ransomware threat actors often use data exfiltration to harbor an organization’s data for extended periods.
This power to extort the organization again, or release proprietary and sensitive data to the public, can lead to long-term costs or reputational damage.
Read more on eSecurity Planet: How to Prevent Ransomware Attacks: 20 Best Practices

How to Protect Against Ransomware
Protecting against ransomware means developing a cybersecurity model equipped to fend off common and advanced malware strains — and when the worst happens, having the necessary backups to recover from data loss due to encryption. Guarding against future threats also means conducting proper forensic analysis of past disruptions and existing vulnerabilities.
Critical tools and best practices for ransomware protection include:
Network Security Tools
- On-premises, virtual, cloud, and offline data backups
- Next-generation antivirus (NGAV)
- Next-generation firewalls (NGFW)
- Detection and response (EDR, MDR, NDR, XDR)
- Vulnerability scanning and patch management
- Intrusion detection and prevention system (IDPS)
- Security information and event management (SIEM)
- Zero trust network access (ZTNA) and microsegmentation
Cloud Security Tools
- Cloud access security broker (CASB)
- Cloud workload protection platform (CWPP)
- Cloud security posture management (CSPM)
- Cloud-native application protection platform (CNAPP)
How to Choose a Ransomware Protection Solution
Ransomware protection is about much more than a single product or solution. Organizations should consider the above tools part of the jigsaw puzzle, rather than inclusive ransomware protection. The best so-called ransomware protection solutions are those efficiently securing users, applications, and network segments from advanced malware threats.
Real-time and early detection capabilities are critical for zero-day threats, so vendors with the latest XDR technology, behavioral analysis, and global threat intelligence are a customer’s best bet.
Read next: Best Server Monitoring Software & Tools

