The server is an essential element in every organization’s IT infrastructure. Apart from holding a lot of critical information and resources, it powers an organization’s internet connectivity, allows access to remote employees, facilitates communication among systems, and more. All these resources can be protected from malicious actors using server security tools.
Server security tools help organizations protect server resources against intrusions, malware attacks, and other forms of malicious actions. In this article, we will help you choose the right server security solution for your organization in 2023.
- Malwarebytes: Best overall (Read more)
- Avast Server Antivirus: Best for Windows servers (Read more)
- Syxsense Cortex: Best for ease of use (Read more)
- Barracuda XDR Server Security: Best for brandable reporting (Read more)
- Delinea Server Suite: Best for privileged access management (Read more)
- WithSecure: Best for policy management (Read more)
- Sophos Intercept X: Best for server-to-container protection (Read more)
Top server security tools comparison
The table below highlights the key features of server security solutions and their pricing details.
| File backup | Unified dashboard | Multiple platform support | Reporting features | Starting price | |
|---|---|---|---|---|---|
| Malwarebytes | Yes | Yes | Yes | Yes | $150/yr per device |
| Avast Server Antivirus | Yes | Yes | Windows only | Yes | $39.21/yr per device |
| Syxsense Cortex | Yes | Yes | Yes | Yes | Pricing is provided upon request |
| Barracuda XDR Server Security | Yes | Yes | Windows and Linux | Yes | Pricing is provided upon request |
| Delinea Server Suite | No | Yes | Windows, Linux, and UNIX | Yes | Pricing is provided upon request |
| WithSecure | Yes | Yes | Windows, Citrix, and Terminal | No | Pricing is provided upon request |
| Sophos Intercept X | Yes | Yes | Windows and Linux | Yes | Pricing is provided upon request |
Jump to:
- Key features of server security tools
- How to choose the best server security tool for your business
- Frequently asked questions (FAQ)
- Methodology

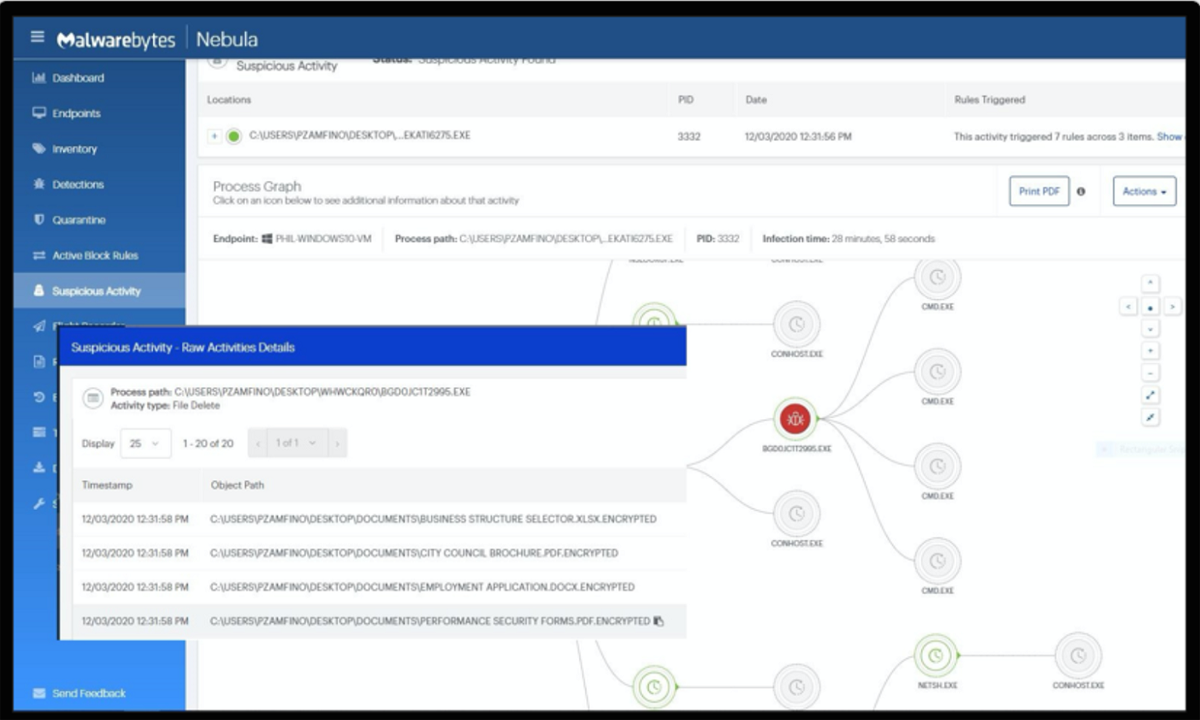
Malwarebytes
Best overall
Malwarebytes Endpoint Protection for Servers provides malware protection and remediation for the server infrastructure. It is delivered from a single cloud console that provides visibility into all servers and workstations.
Malwarebytes has a lightweight design and offers cross-platform support for Windows, Linux, and Mac endpoints. Also offered as a cloud-based platform, the tool allows users to manage and analyze endpoint processes, registry, and network activities in the cloud.
Other notable server security features in Malwarebytes include network isolation, server isolation, and process isolation. In addition, there is ransomware rollback, which activates file backups in the event of an attack.
Pricing
Pricing starts at $150 per device per year.
Features
- Known and unknown malware detection.
- Behavioral monitoring and machine learning profiles threats across web, memory, application, and files.
- Linking Engine traces every installation, modification, and process instantiation.
- Cloud-based dashboard delivers real-time status of events and device health.
Pros
- Transparent pricing and availability of demo for users to check out the tool.
- Activates file backups in the event of an attack.
- Offers multi-platform support.
- Supports visibility into servers and workstations from a single dashboard.
Cons
- Pricing might be costly for smaller businesses.
- There is no free trial.

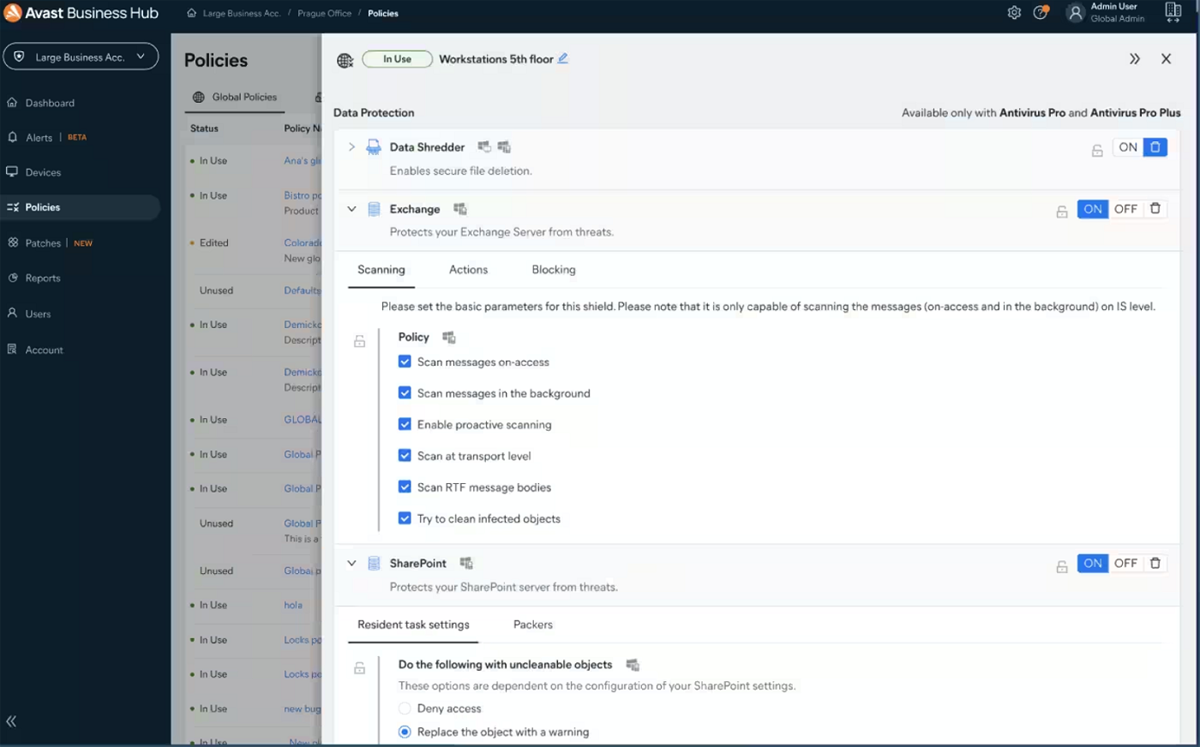
Avast Server Antivirus
Best for Windows servers
Avast antivirus for servers comes with the Avast Essential Business Security solution, also known as Business Hub. Through an online management platform, users can set up the solution, monitor the health of their server devices, and manage subscriptions for the platform.
The tool also comes with malware scanning capability for inspecting server downloads and uploads, server threat detection capability, and a global policy feature for setting security rules on how available services work on endpoints in your network.
Also included in the Avast server security solution is SharePoint Server Protection, which helps users check for malware in all files uploaded to shared storage. There is also Exchange Server Protection that scans and filters emails at the Exchange server level.
Pricing
Avast Server Antivirus is included with their Essential Business Security package, starting at $39.21 per device per year.
Features
- CyberCapture feature for suspicious threat analysis.
- Exchange Server Protection.
- SharePoint Server Protection.
- Comes with add-ons like patch management.
- Antivirus for Linux servers can be purchased as an optional add-on.
Pros
- Protects servers, data, devices, applications, and networks.
- Monitors alerts and threats in real-time from a single dashboard.
- Gathers key data and generates detailed activity reports.
- Offers 30-day free trial.
Cons
- Only compatible with Windows Servers unless you purchase the additional Linux add-on.
- Users might experience some downtime during installation.

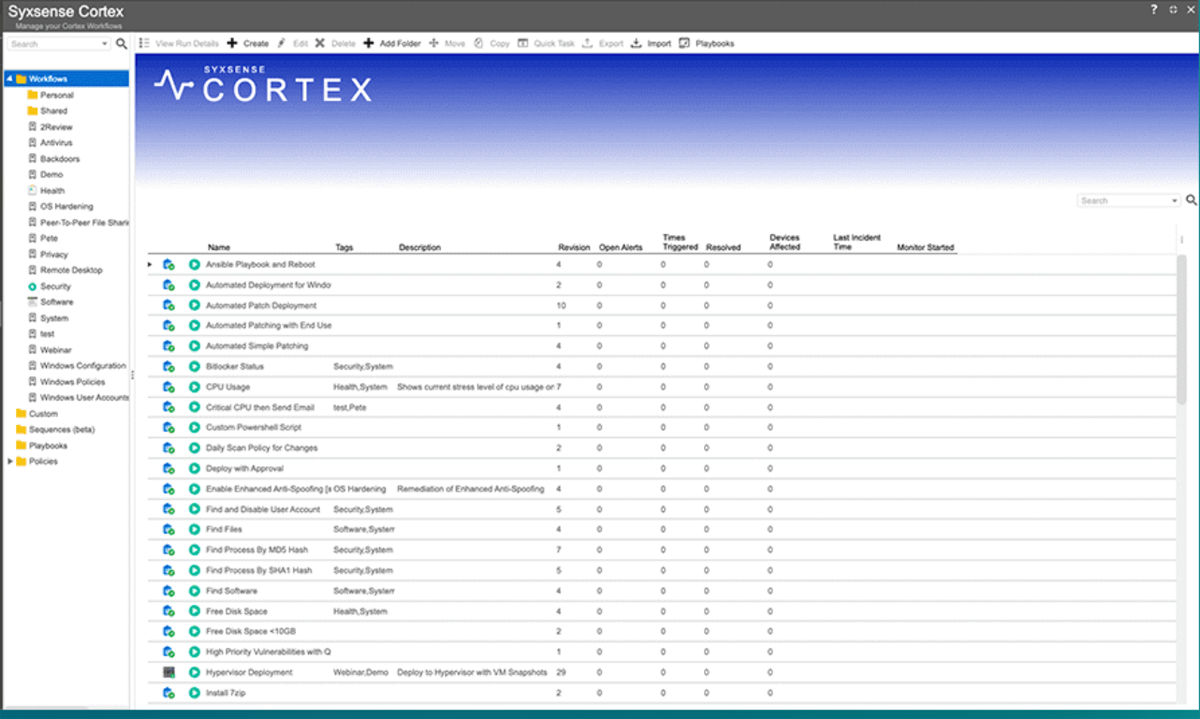
Syxsense Cortex
Best for ease of use
Syxsense Cortex provides up-to-date server patching and IT management; a larger suite includes vulnerability scanning. The solution offers an easy management dashboard with its drag-and-drop interface.
With this tool, IT and security teams can monitor things like CPU and RAM and disk space usage on any device, as well as have access to a customizable reporting tool to analyze reports. In addition, Syxsense offers IT teams prebuilt templates for server monitoring and patching. The tool also provides prebuilt vulnerability scripts to help users with remediation workflows, reducing the need to create new workflows.
Pricing
Syxsence offers a 14-day free trial. Contact the vendor for a quote.
Features
- Automatically deploy OS and third-party patches, as well as Windows 10 updates.
- Consolidates desktop, laptop, and server patching into a single console.
- Document patching and reporting to meet PCI DSS, HIPAA, and SOX compliance.
- Patch rollback in case a patch causes a configuration issue.
- Patch supersedence enables newer patches with a high-priority status to be installed first.
- Automation of patch distribution to avoid tying up network bandwidth.
- Scans authorization issues, security implementation, and antivirus status.
Pros
- Availability of free trial.
- Supports customizable reporting for easy proof of compliance.
- Single-pane visibility.
- It can be managed through a web browser.
Cons
- There is no transparent pricing plan.
- Poor documentation of the server security solution.

Barracuda XDR Server Security
Best for brandable reporting
Barracuda XDR Server Security is another popular server security tool for Windows and Linux servers. Users can monitor and identify risks using Barracuda XDR and Security Operations Center.
The solution’s threat detection feature, which is overlaid in the MITRE ATT&CK framework, can provide visibility into attack tactics, show the way an attack is likely to move, and reveal gaps in coverage. In addition, users are provided with a customizable reporting feature to enable them to brand their reports.
Pricing
Contact Barracuda for a quote.
Features
- Supports Windows and Linux servers.
- Customizable reporting.
- Centralized visibility.
- SIEM and SOAR analysis.
Pros
- Offers visibility into all cloud environments.
- Opportunity to partner with Barracuda’s SOC team for guidance.
- Availability of webinars and demos to aid usability.
Cons
- Organizations may need to rely on Barracuda’s team of security analysts for real-time threat monitoring.
- No transparent pricing details.

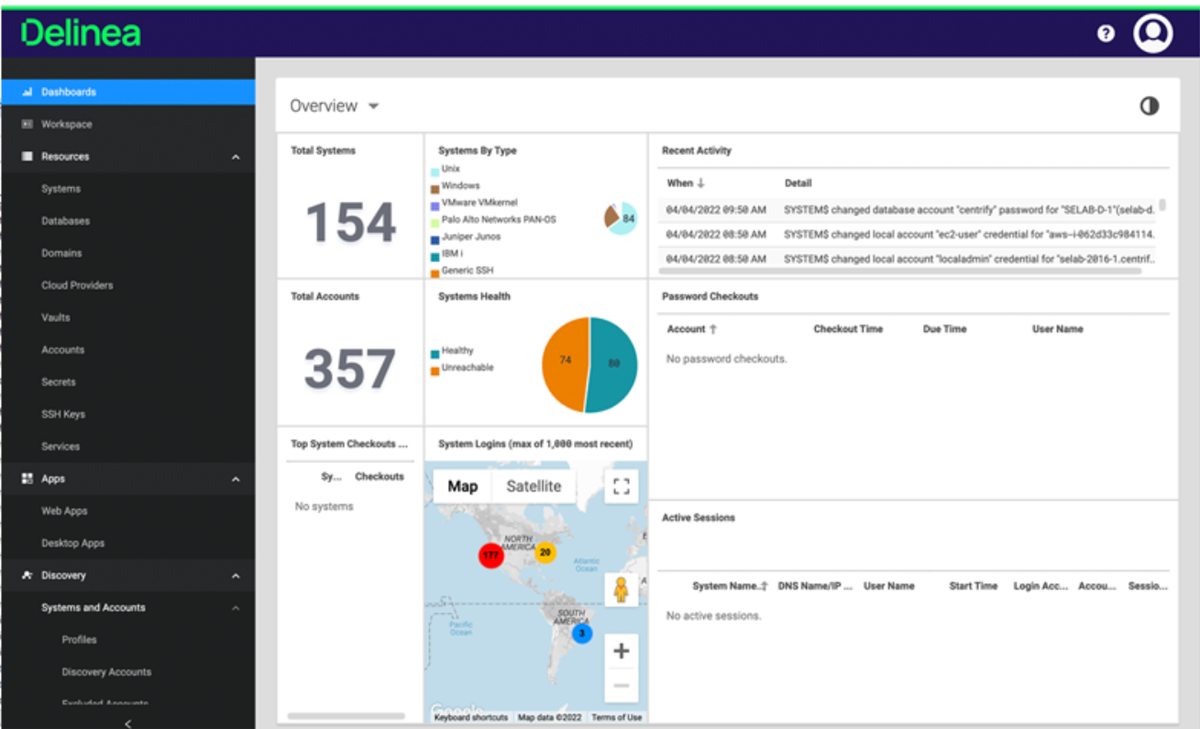
Delinea Server Suite
Best for privileged access management
Formerly known as Centrify, Delinea Server Suite is a powerful server security tool that focuses on offering privileged access management at the server level. It offers a central dashboard where users can execute least privilege practices for servers and manage policies from Active Directory. This server security tool can be used to unify policy management for Linux, Windows, and UNIX platforms.
With the solution, users can establish trusted Active Directory machine identities for authentication, helping them implement special privileges, multifactor authentication (MFA), and remote access security.
Pricing
Contact the vendor for a quote.
Features
- Active directory bridging.
- Authentication policy management.
- MFA enforcement at login and privilege.
- Host-based session recording, auditing, and reporting.
- Group policy management.
Pros
- Supports centrally managed identities.
- Allows users to enforce least privilege practices.
- Users can enforce adaptive MFA.
- Supports complete audit trail for security review.
Cons
- No transparent pricing details.
- No demo version provided.

WithSecure
Best for policy management
WithSecure is anti-malware software designed specifically for Windows, Citrix, and Terminal servers. This suite offers advanced real-time defense against a wide range of malicious software, including viruses, Trojan horses, spyware, rootkits, and other forms of malware against servers. Users can manage the software through either the Policy Manager or the built-in Web Console, allowing for centralized and local control of the security settings.
The tool comes with DeepGuard technology for behavior-based detection of new threats, a software updater for keeping the operating system and third-party servers up to date, and a botnet blocker.
Pricing
Pricing details are only provided upon request.
Features
- Microsoft file server protection.
- Offload scanning agent.
- Web traffic scanning.
- Software updater.
- Botnet blocker.
Pros
- It can be managed through the Policy Manager or the built-in Web Console.
- Offers real-time scanning protection.
- Supports update management for both the host system and third-party server software.
Cons
- No pricing details provided.
- Inadequate information on its free trial.
- No demo version provided.

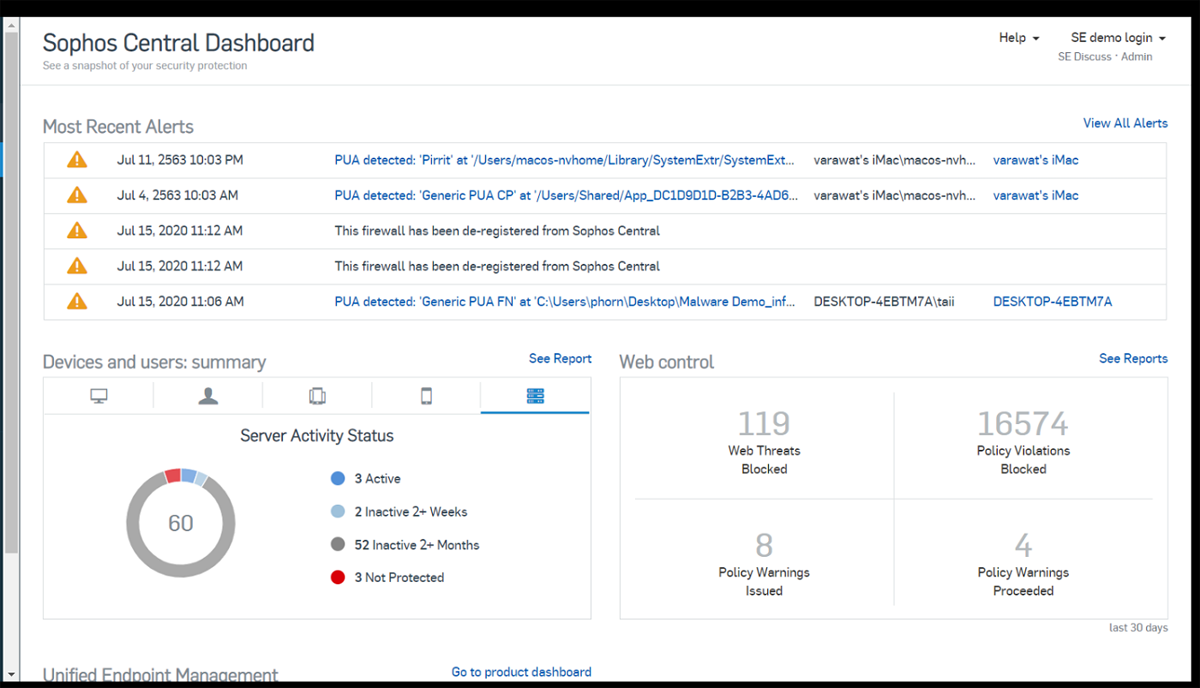
Sophos Intercept X
Best for server-to-container protection
Sophos Intercept X offers server workload protection and container security for cloud, data centers, and on-premise. The solution provides visibility across your on-premise, cloud, and virtual server workloads.
Intercept X is powered by artificial intelligence, which makes it possible to detect known and unknown malware on the server. Users can also go beyond server protection by using Extended Detection and Response (XDR) to incorporate cross-platform data for extended visibility. With its Linux Detection capability, users may not need a kernel module, baselining, orchestration, and system scans to detect attacks on their servers.
Pricing
Quote is provided upon request.
Features
- Extended detection and response.
- Server lockdown capability.
- Deep learning malware detection.
- Malicious Traffic Detection (MTD).
- Server-to-container protection.
- Server-specific policy management.
Pros
- Supports automatic file recovery.
- Offers behavior analysis for preventing boot record attacks.
- Offers automated malware removal.
Cons
- Activity Reporting is only available in the higher plans.
- No transparent pricing details.
- Limited information on the free trial.
Key features of server security tools
Server security solutions come with a lot of features. Though the exact list will vary between each solution, some of the core features to look for include real-time threat detection, intrusion prevention, vulnerability assessments, and patch management.
Real-time threat detection
A key aspect of security is catching threats in real-time. Advanced security solutions employ sophisticated algorithms and machine-learning techniques to analyze server activity non-stop.
This makes for efficient monitoring of inbound and outgoing network traffic, user authentication attempts, and application behavior to identify suspicious patterns or potential signs of malicious activity on the server.
Intrusion prevention systems (IPS)
An IPS is a crucial component of server security tools that acts as a proactive defense mechanism. IPS goes beyond simple threat detection to actively block and mitigate potential threats.
When the security tool identifies suspicious network activity or any pattern of intrusion attempts, the IPS automatically enforces access controls and security policies to prevent unauthorized access to the server.
Vulnerability assessment and patch management
The dynamic landscape of cybersecurity demands continuous evaluation of server vulnerabilities and the prompt application of security patches. That’s why top server security tools also come with vulnerability assessment capability that scans the server infrastructure for potential weaknesses.
Depending on the sophistication of the tool, this feature can identify known and unknown vulnerabilities in server software, operating systems, and applications. The feature can also provide administrators with actionable insights to prioritize patch management effectively in order to keep servers up-to-date.
Encryption and data protection
Data security is paramount in server environments, especially when handling sensitive information. Encryption plays a vital role in ensuring data confidentiality, even if attackers manage to gain unauthorized access to the server. Quality server security tools often provide strong encryption protocols like SSL/TLS to safeguard data at rest and in transit.
Centralized management and reporting
Managing security across multiple servers can become overwhelming without centralized management capabilities. Most server security tools provide a centralized dashboard or console where administrators can monitor the security status of all servers in the infrastructure from a single interface. This feature allows for streamlined configuration, deployment of security policies, and monitoring of security events across the entire server network.
Additionally, comprehensive reporting capabilities are essential for tracking security incidents, analyzing trends, and complying with regulatory requirements.
How to choose the best server security tool for your business
Choosing the best server security tool for your business requires careful consideration of several key factors. Firstly, you should assess your business’s specific security needs and infrastructure. Doing this will help you identify the types of servers you use, the critical data they store, and the potential threats you may face.
Look for a server security tool that offers comprehensive protection, including real-time threat detection, intrusion prevention, vulnerability assessment, encryption, and centralized management. Scalability is also crucial, as your business may grow, and you’ll want a solution that can adapt to changing requirements.
Additionally, consider the tool’s compatibility with your existing systems and the possibility of integration with other systems to avoid disruptions and minimize the learning curve for your IT team. You should also prioritize solutions that provide regular updates and excellent customer support to ensure your security remains up-to-date and effective in the face of emerging threats.
Frequently asked questions (FAQ)
How does server security software work?
Server security software acts as a defense system by employing various security measures such as firewalls, intrusion detection systems, antivirus scans, and access controls to safeguard servers from unauthorized access and data breaches.
What is the benefit of using a server security tool?
Using a server security tool helps organizations protect their server infrastructure against unauthorized access and data breaches, safeguard sensitive information, and minimize the risk of costly downtime.
Can server security tools work across different server environments, including on-premises and cloud-based systems?
Yes, many server security tools are designed to work across different server environments, including on-premises and cloud-based systems.
Methodology
We conducted a comprehensive evaluation of the leading server security tools by analyzing resources provided by each vendor on their website. We also utilized the information provided by verified users on reliable review sites.
Some of the features we prioritized during our review include user-friendliness, compatibility with other systems, server security functionalities, and availability of relevant resources for potential users. Wherever possible, we engaged with video or hands-on demo tools to get a better picture of how each of the tools work.
Bottom line: Protect critical data and function with server security tools
As the threat landscape continues to evolve, it is crucial for businesses to adopt a proactive approach to server security. Fortunately, the tools mentioned in this article can serve as essential components of a comprehensive server security strategy.
However, it is important to remember that no tool can be a one-size-fits-all solution for your server solution. Effective server security requires a multilayered approach that combines cutting-edge technologies with skilled cybersecurity professionals.
Additionally, staying up-to-date with the latest security trends and regularly patching software vulnerabilities are critical for maintaining a robust defense posture.
Protect your servers against insidious SQL injection attacks with our guide to the best SQLi detection tools.




