Static Application Security Testing (SAST) is often used to scan the source, binary, or byte code of an application. As well as identifying the root cause of vulnerabilities, it helps to remediate any underlying security flaws and provides feedback to developers on any coding problems. The major benefit is to have more code created with fewer vulnerabilities.
Read more: Top 5 Cybersecurity Certifications to Advance Your Career
Top SAST Tools
ServerWatch evaluated many SAST tools. Here are our top picks in no particular order.
WhiteSource Software
WhiteSource Cure is a security auto-remediation application designed for custom code. It replaces vulnerable code with fixed secured code by offering developers remediation suggestions for security vulnerabilities. WhiteSource Cure offers a remediation-centric approach that goes beyond detection, acting as a developer’s security expert to help speed up the release of secure software.
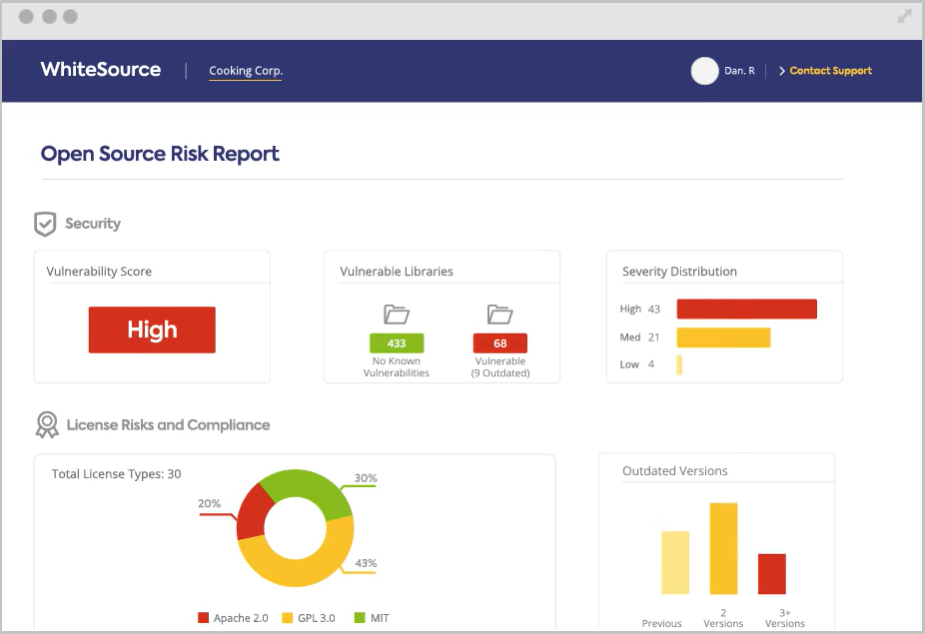
Key Differentiators
- Provides a customized report with actionable remediation suggestions for vulnerabilities detected in public projects
- Suggestions are presented on the vulnerable code itself and can be used as-is in developers’ IDE
- Developers can review and accept the proposed secure code, applying a fix at the click of a button
- Suggestions are case-specific
- Helps AppSec experts scale security, reducing the need to train developers
- Closes the gap from detection to remediation, providing a shift left security solution that lightens developers’ load
Perforce
Perforce SAST offerings consist of two tools, Klocwork and Helix QAC. These tools provide developers complete coverage of coding standards, security compliance, and safety compliance. Perforce SAST tools support most of the development languages, including C, C++, C#, Java, JavaScript, and Python. Developers can use the SAST tools within their IDEs like visual studio code, IntelliJ, and others.
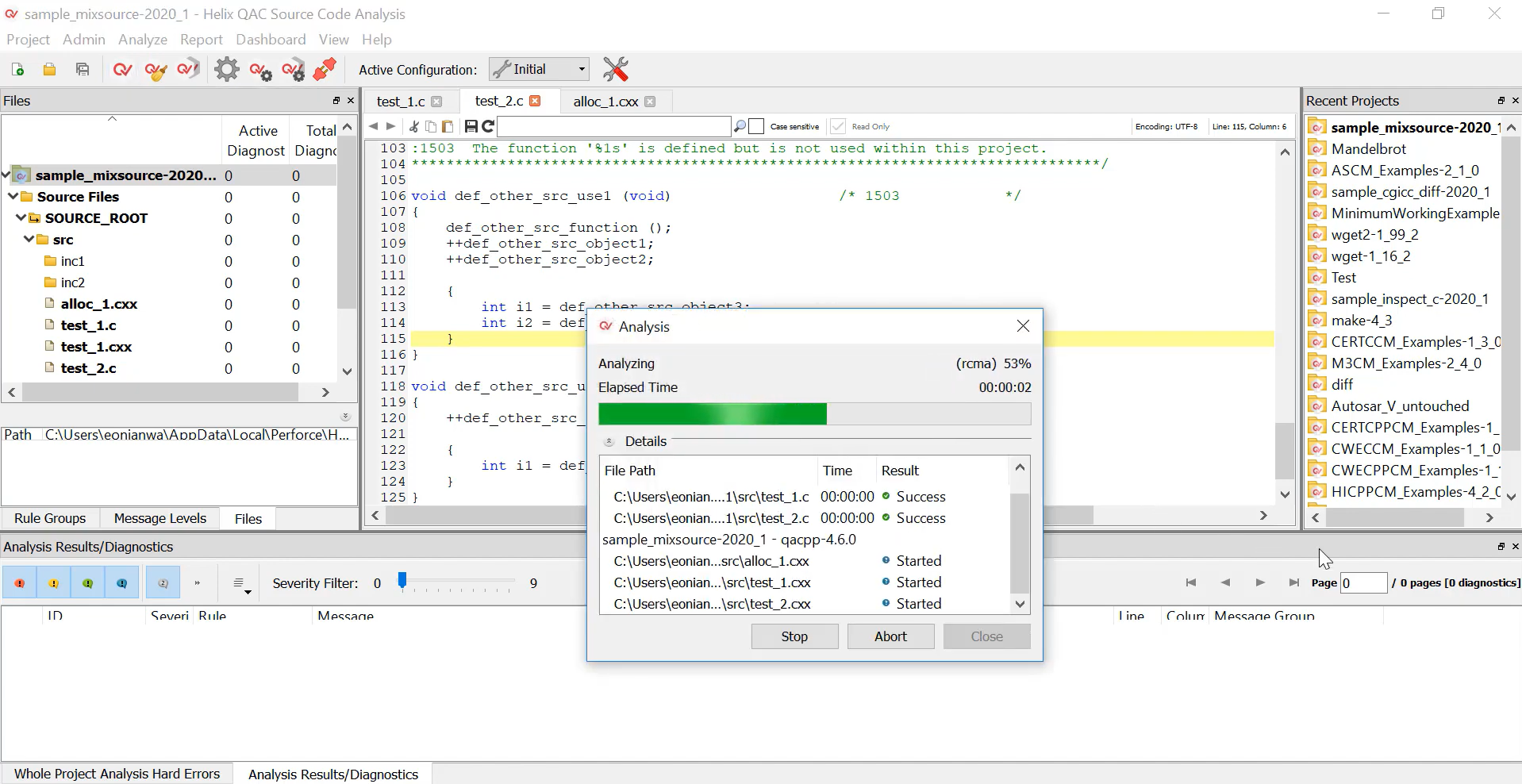
Key Differentiators
- Ability to scan massive code bases (millions of lines of code)
- Quickly and accurately provides analysis across different languages
- Incremental and differential analysis, which only scans the changed code areas and enhances feedback loops
- Can generate compliance reports for audits, including MISRA and AUTOSAR, for various verticals
- Can integrate into CI/CD tools like Jenkins, as well as IDEs, and can also be run within Docker containers
- Dashboards offer details of the various security and compliance issues, as well as links for training and remediation
- Integration with the security training platform Secure Code Warrior for dev training and awareness around code security standards
CyberRes
CyberRes Fortify includes both static and dynamic application security testing technologies, along with runtime application monitoring and protection. Developers can use the SAST tool to find and fix security defects in real-time during the coding process, with integrations to IDEs such as Eclipse or Visual Studio.
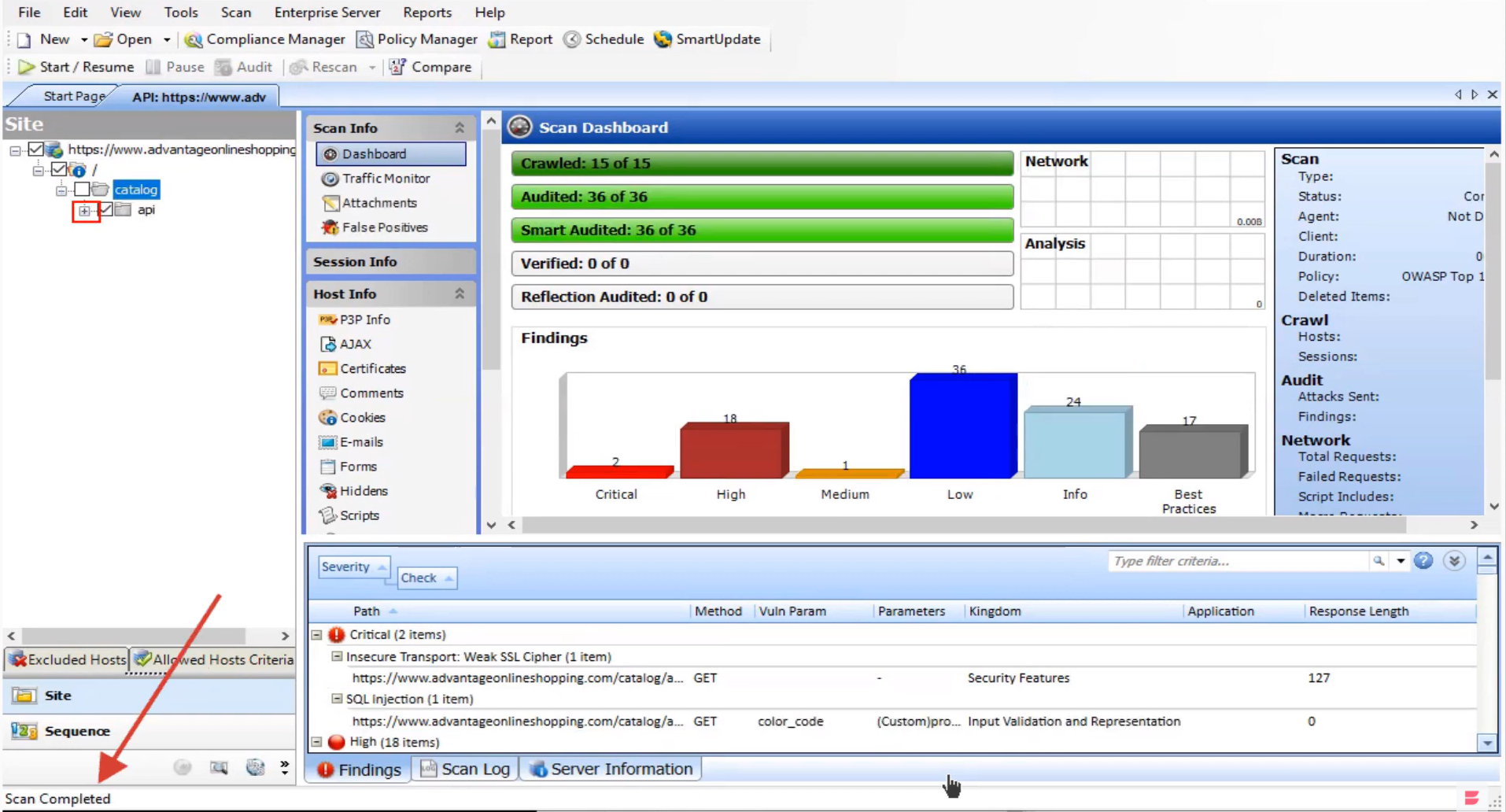
Key Differentiators
- Gamified training supports developers’ ability to create secure code
- Solutions can be deployed in-house or as a managed service to build a scalable Software Security Assurance program
- Support for 27 major languages and their frameworks, with agile updates
- 810 vulnerability categories for SAST that enable compliance with standards such as OWASP Top 10, CWE/SANS Top 25, DISA STIG, and PCI DSS
- Fortify Static Code Analyzer identifies exploitable security vulnerabilities in source code
- Fortify on Demand Application security as a service with security testing, vulnerability management, expertise, and support
- Fortify Software Security Center integrates and automates security testing with dev
SonarQube
SonarQube empowers developers to write cleaner and safer code. It encompasses an open-source community of more than 200,000 development teams. Thousands of automated Static Code Analysis rules protect apps.
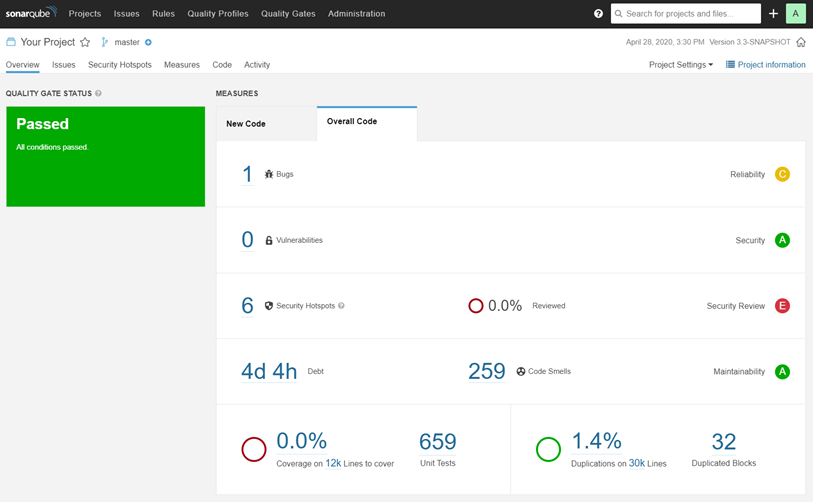
Key Differentiators
- Catch bugs to prevent undefined behavior from impacting end users
- Fix vulnerabilities that compromise apps, and learn AppSec along the way with Security Hotspots
- Supports languages like Java, Python, Swift, COBOL, Apex, PHP, TS, JS, C++, C, C#, and more
- CI/CD integration including Jenkins, Azure DevOps server, and others
- SonarQube can analyze branches and notify of issues to address
Spectral
SpectralOps scans the entire SDLC for hard-coded secrets, keys, and misconfigured code, continuously. It is a multi-language AI-driven SAST. The primary objective is to prevent secrets (credentials, API keys, encryption keys, etc.) from leaking, as they tend to be hard-coded at the early stages of development.
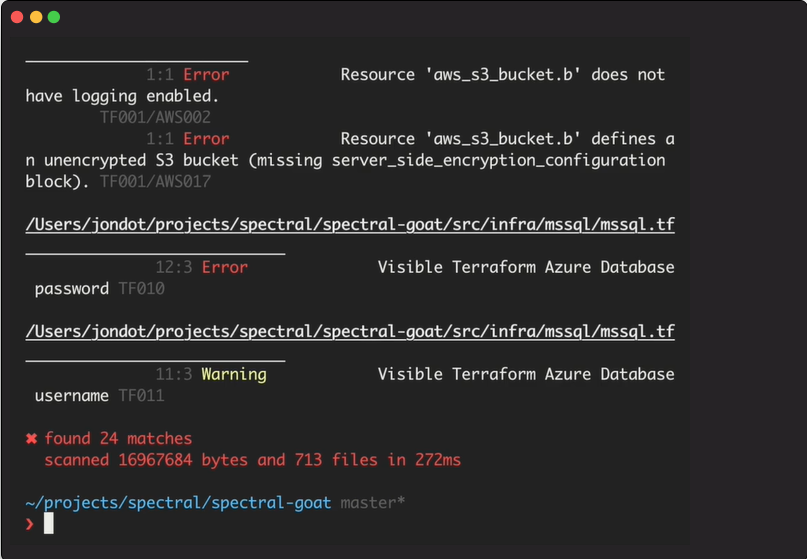
Key Differentiators
- Monitor, classify, and protect code, assets, and infrastructure for exposed API keys, tokens, credentials, and high-risk security misconfigurations
- SpectralOps avoids false positives by using AI
- Continuously uncover and monitor public blind spots, supply chain gaps, and proprietary code assets across multiple data sources
- Over 2000 detectors to discover and classify data silos and uncover data breaches before they happen
- Get real-time Slack alerts, JIRA tickets, or your choice of notification on data breaches in real time
Checkmarx
Checkmarx supports many languages out of the box with no configuration. It identifies security issues and offers solutions. With Checkmarx SAST, you can run fast incremental or full scans whenever needed.
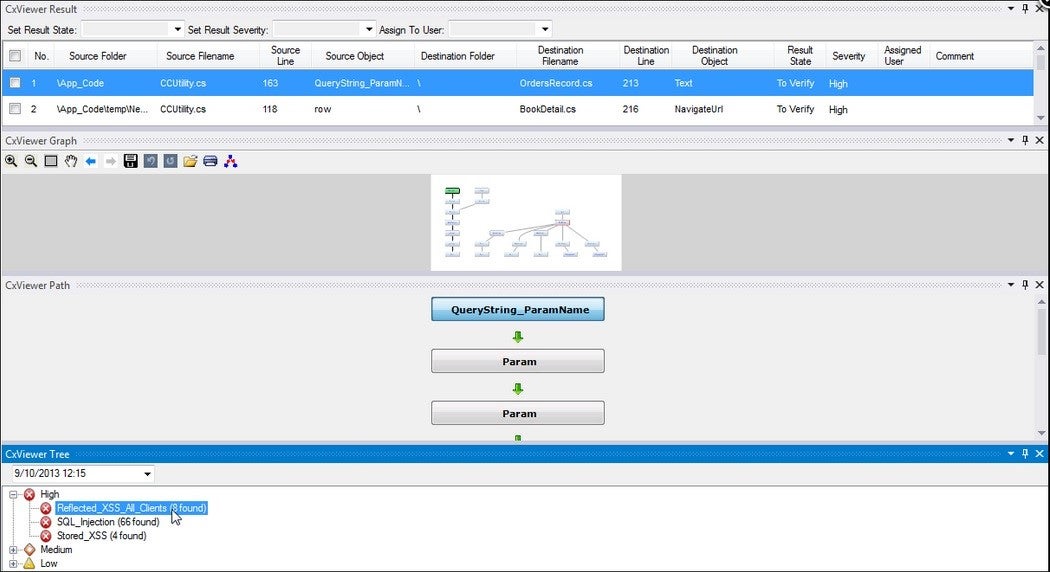
Key Differentiators
- Injects security automation into the dev pipeline
- Handles the most complex coding environments
- Scales security with flexible scanning in 25+ languages and frameworks
- Fixes problems fast, with few false positives and fire drills
- Uncovers critical vulnerabilities early in the CI/CD pipeline
- Automatically scans uncompiled source code for vulnerabilities
- Integrates with mainstream IDE, CI server, source code management platform, etc.
- Customizable queries and insights
Veracode
Veracode Static Analysis for SAST has a low false-positive count and offers developers potential solutions to issues it finds. As it is a Software-as-a-Service solution, there is low setup overhead and a quick turnaround from acquiring access and getting results.
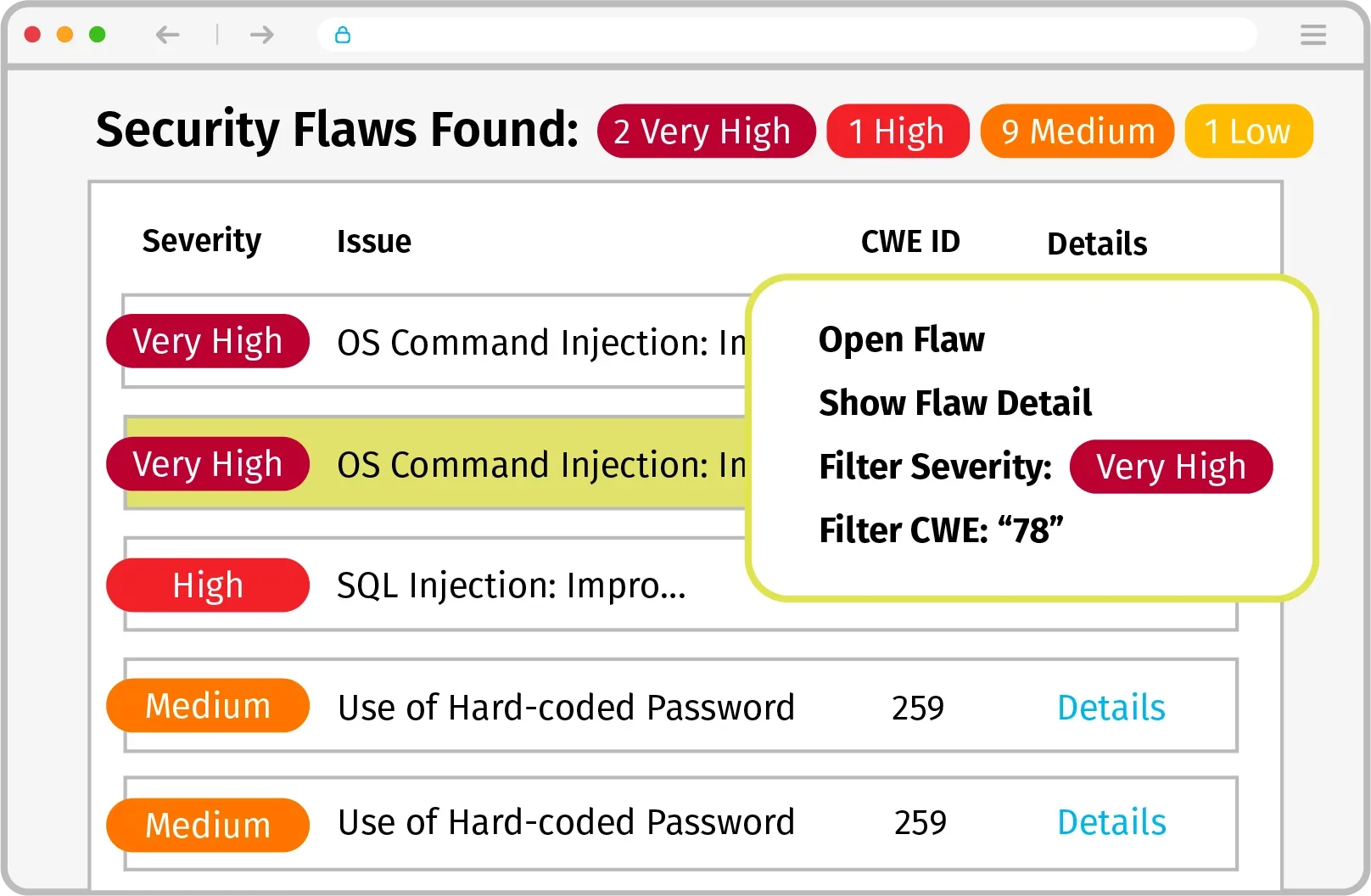
Key Differentiators
- Simplifies AppSec programs by combining five application security analysis types into one solution integrated into the development pipeline
- Through automated, peer, and expert guidance, developers get the tools and skills to keep the AppSec program on track
- Manages risk and satisfy reporting and compliance requirements without interrupting developer workflows
- Reduces remediation time from 2.5 hours to 15 minutes
- Simplifies vendor management and reporting
Reshift
Reshift is a more specialized SAST offering, specifically built for NodeJS. The approach is to fix errors as early as possible. By integrating into IDEs and CI/CD pipelines, Reshift makes sure to test code as soon as it is typed.
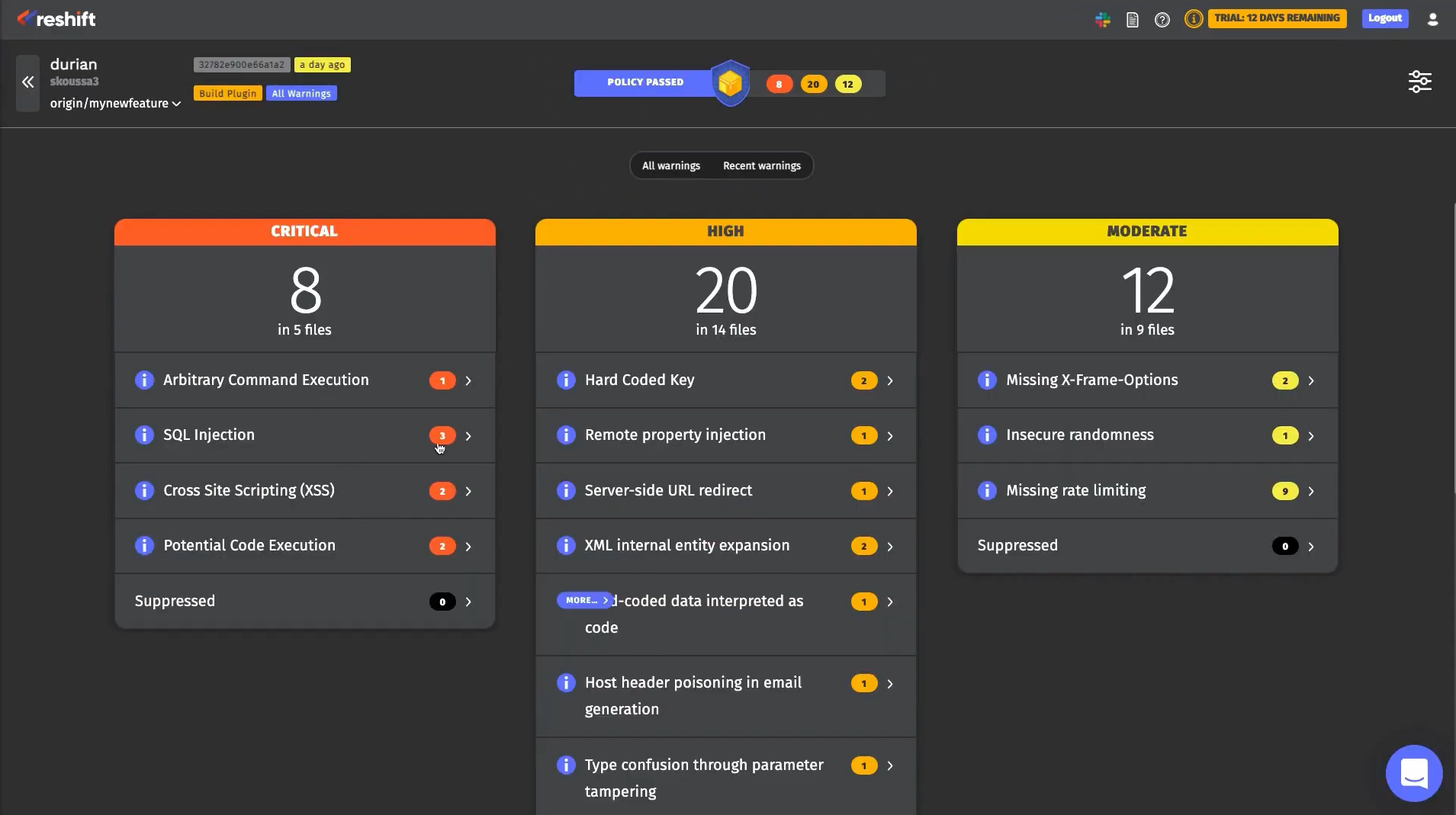
Key Differentiators
- Reshift has a free version for a single user
- Fixed price scale based on every 10 users
- Integrates with the developers’ IDE, so security issues are found in real time and fixed before the code is merged
- Reshift is designed for SMBs, making it easy to set up with no need for security expertise
- Improve code security while learning about secure code
Read more: Best Server Security Services
What Is Static Application Security Testing?
SAST is a mature application security testing method, where source code is analyzed from the inside out while components are at rest. It scans in-house code and design to detect flaws that are indicative of weaknesses that could lead to security vulnerabilities.
SAST doesn’t scan dynamic code. It focuses on static code and tests code at rest, without having to run it. That makes it easy to use at the coding and testing stages of development, integrating into Continuous Integration (CI) servers and, more recently, into integrated development environments (IDEs).
The scans done by SAST tools are based on predetermined rules that define coding errors to assess and address. These scans are very good at identifying common security vulnerabilities such as SQL injection, input validation, and stack buffer overflows.
SAST has limitations, however. It is good at finding problems within the code, but not vulnerabilities outside the code in areas such as APIs. That requires a different approach known as Dynamic Application Security Testing (DAST). There are also other related tools known as Mobile Application Security Testing (MAST), and Interactive Application Security Testing (IAST).
What Is the Difference Between SAST and DAST?
SAST methods are generally used early in the development cycle to test the application from the inside out (also known as white box testing). No need to have perform the code analysis on a running system; these tools test line-by-line.
DAST, on the other hand, is a black box testing approach that is done while the application is running, taking an outside-in approach. DAST makes attempts to penetrate the application to identify vulnerabilities. Its testing encompasses bugs outside the code and in third-party interfaces, source code, byte code, and binaries — which usually makes such analysis easier to use and less expensive than SAST.
However, DAST tools may not be able to isolate the exact site of a weakness in the code. Thus, it is probably best to adopt a hybrid analysis testing method that combines both SAST and DAST.
Read next: Top DAST Tools: Dynamic Application Security Testing

