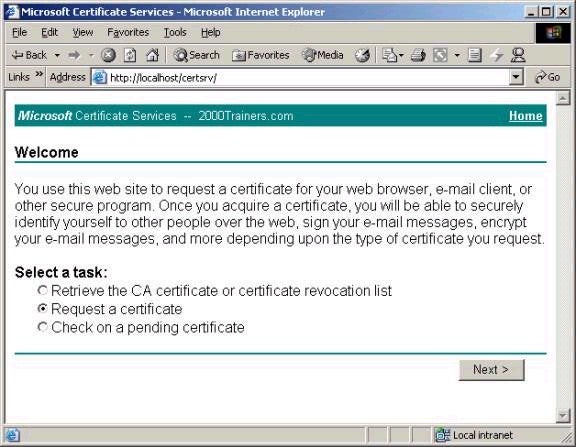
Once
Certificate Services is installed, the Server is ready to
accept certificate requests from clients. For a Standalone
CA these requests must be made a web browser by accessing
the certificate server using the URL http://computername/certsrv.
A wizard that walks you through the process step-by-step
handles the actual request process.
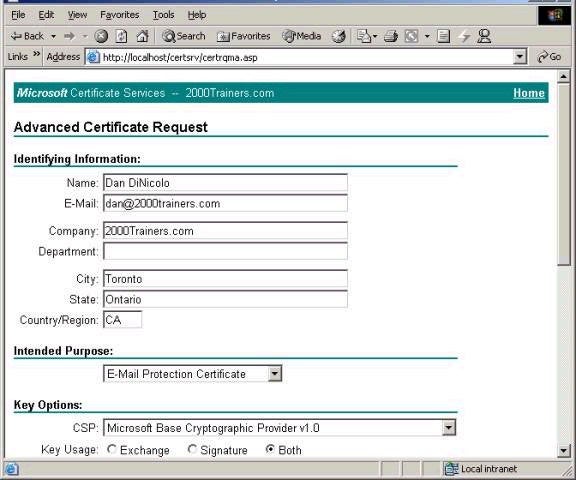
The certificate request process also includes providing
information about the user, the use of the certificate,
and so forth. In the example below, I am requesting a
certificate to secure email.
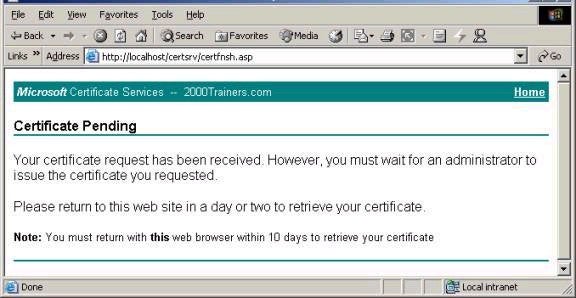
After the request is completed, the user is presented with the
following message. Note that the request has been made,
but the certificate will not be issued until approved by
the Administrator.
The approval process for a requested certificate is pretty
straightforward. Using the Certificate Authority tool in
Administrative Tools, open the Pending Requests option,
and choose to Issue the certificate or deny the request,
as shown below.
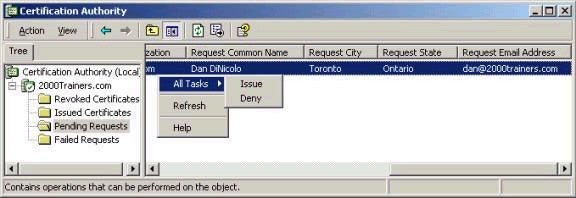
Note that once completed, the user can again access the Certificate Services web site and download and install their new certificate. The certificate just issued will now be found in the Issued Certificates section from the screen above, and can be revoked from this interface as well. In an Active Directory environment, note that users can also request certificates using the Certificates MMC snap-in, or can be configured for auto-enrollment of certificates (on both a user and computer basis) via Group Policy. In large environments running an Enterprise CA, this is often the most practical idea.
Integration with Group Policy
It is obvious that setting up a PKI involves much planning and is a great deal of work. I couldn’t possibly go into all of the details of PKI management in this article, not without possibly writing a dedicated book. However, the 70-240 exam doesn’t assume you’re a cryptography expect, so I’m not going to move far beyond the basics (for a longer and more detailed overview I would suggest reading http://www.microsoft.com/windows2000/docs/PKI.doc). One of the main benefits of setting up Certificate Services as an Enterprise CA is not only its integration with Active Directory, but also the ability to manage much of the necessary dirty work via Group Policy settings that handle automatic certificate requests, also known as auto-enrollment. In fact, Windows 2000 Group Policy will allow you to do the following:
– Have domain client computers automatically request and install a computer certificate. This certificate identifies the computer and can be used for the purpose of IPSec encryption / authentication, and is also a requirement for L2TP-based VPN connections (since both the user and computer must be authenticated in those connections). This is accomplished in the Computer Configuration – Windows Settings – Security Settings – Public Key Policies – Automatic Certificate Request Settings section of Group Policy. Any systems to which this policy applies will automatically request, download and install their certificate.
– Create and distribute certificate trust lists. This will allow client computers to be easily configured with a list of trusted Root CAs and their associated hierarchies. This is done via Computer Configuration – Windows Settings – Security Settings – Public Key Policies – Enterprise Trust in Group Policy. The actual configuration is handled via the Certificate Trust List wizard.
– Establish trust with other external root authorities, for example ones that are not part of your organization. This could be useful in secure partnering relationships between organizations. These are configured in Group Policy under Computer Configuration – Windows Settings – Security Settings – Public Key Policies – Trusted Root Certification Authorities.
– Adding encrypted data recovery agents for the purpose of using the Encrypted File System (EFS). Although the Administrator account is there by default, others can be added by accessing Computer Configuration – Windows Settings – Security Settings – Public Key Policies – Encrypted Data Recovery Agents.
And so ladies and gentlemen, we have finally reached the end of a very long road. All that is left now if for you to brush up on those areas where you feel the need, and then get to writing the big exam. Congratulations to all of those who have contacted me telling me of their success on the exam – I told you it wasn’t that hard, as long as you know your stuff. My sincere best wishes to all of you have decided to stick with writing the 70-240 exam even though you now know that your old NT 4.0 certification is still valid – I sincerely believe that in studying and doing the exam you are doing yourself justice, rather than using the change as an excuse not to challenge yourself. Thanks so much to everyone who has supported the series, and those whose emails of support kept me plugging away at the articles as time permitted. Thanks also to those who have been understanding of the delays on my end due to my work in Africa, and thanks for the kind words with respect to that as well. Without rambling, just thank you. I feel confident that each and every one of you who have prepared for the exam can pass. Though time is running short, its still not too late to take advantage of the opportunity presented to you. If I can offer some parting words for the series – forget about the piece of paper, focus on learning, and you can’t really lose.
Best of luck with your studies,
Dan

