A Network Policy Server (NPS) allows network administrators to create and enforce policies for network access, ensuring that only authorized users and devices can access network resources. This versatile tool plays a key role in centralized authentication, authorization, and accounting for users and devices that connect to a network.
Essentially, NPS is Microsoft’s implementation of a Remote Authentication Dial-In User Service (RADIUS) server and proxy in the Windows Server operating systems. It is a crucial component in network management and security.
To better understand NPS, we’ll first take a look at what RADIUS servers are, then explore the purpose of NPS, its benefits, its role in networking, and best practices for managing an NPS.
Table of Contents
What is the importance of network security and policy management?
With the increasing reliance on technology and the internet for business operations, data exchange, and communication, networks and servers have become primary targets for cyberthreats. This elevated risk landscape underscores the necessity of robust network security and meticulous policy management.
Here are the key reasons why network security and policy management are important:
- Protection against cyberthreats: The foremost importance of network security is the protection it offers against a variety of cyberthreats, such as malware, ransomware, phishing attacks, and unauthorized access. Effective security measures prevent attackers from breaching network systems, safeguarding sensitive data and the overall integrity of the network.
- Data privacy and compliance: Adhering to regulatory standards and protecting personal and sensitive information is crucial. Network security and policy management ensure compliance with laws and regulations, such as GDPR, HIPAA, and others, thereby avoiding legal ramifications and maintaining customer trust.
- Business continuity: Cyberattacks can cause significant downtime, leading to loss of productivity and revenue. A secure and well-managed network minimizes the risk of disruptions, ensuring that business operations can continue unhindered.
- Policy management as a framework: Effective policy management sets a clear framework for how network security is handled within an organization. It defines the protocols for access control, user authentication, data handling, and response to security incidents. This structured approach ensures consistency, efficiency, and adaptability in responding to evolving security threats.
- Adaptability to changing threats: The cyberthreat landscape is constantly evolving, with new vulnerabilities emerging regularly. A robust network security strategy, underpinned by dynamic policy management, allows organizations to adapt quickly to these changes, implementing necessary updates and defenses to stay ahead of potential threats.
What is the RADIUS protocol?
The RADIUS protocol is a networking protocol that provides comprehensive and centralized Authentication, Authorization, and Accounting (AAA) management for users who connect and use a network service.
Since its inception in 1991, RADIUS has become a standard for network access servers responsible for connecting users to networks, playing a pivotal role in managing network access control.
Authentication
The first A in AAA refers to Authentication, or the process of verifying a user’s identity. When a user attempts to access a network, they must provide credentials, such as a username and password.
The RADIUS server checks these credentials against its database to confirm the user’s identity. This process ensures that only legitimate users can access the network.
Authorization
Once a user is authenticated, the next step is Authorization. This process determines what an authenticated user is permitted to do on the network.
For example, an administrator may have different access rights compared to a standard user. RADIUS servers manage these permissions, ensuring users can only access resources appropriate to their authorization level.
Accounting
The final A stands for Accounting, which involves tracking the usage of network resources by users. This includes monitoring the amount of time users are connected, the services they access, and the data they transfer. This information is crucial for billing, auditing, and understanding network usage patterns.
What do RADIUS servers do?
RADIUS operates in a client-server model. The RADIUS client, usually a network access server like a VPN or wireless access point, sends user credentials and connection requests to the RADIUS server.
The server then processes these requests against its user database and policies to authenticate and authorize the user. Post-authentication, it sends a response back to the client, either granting or denying access.
Some of the main features of RADIUS servers are:
- Scalability: RADIUS can handle a large number of authentication requests, making it suitable for both small and large networks.
- Flexibility: It supports various authentication methods, including password-based, token-based, and certificate-based authentication.
- Interoperability: RADIUS is widely supported and can be integrated with a variety of network devices and servers.
- Security: The protocol includes methods for encrypting data, such as passwords, during transmission, reducing the risk of interception by unauthorized parties.
What is the purpose of NPS?
An NPS serves as a critical element within the network infrastructure of many organizations, primarily functioning as Microsoft’s implementation of a RADIUS server and proxy. The overarching purpose of NPS is to centralize and streamline the authentication, authorization, and accounting (AAA) of users and devices accessing a network, thereby enhancing security and management efficiency.
Centralized authentication and authorization
Centralized authentication ensures that all users and devices are verified before gaining access to network resources, enhancing security. Authorization, on the other hand, defines what resources authenticated entities are permitted to use.
Below are how an NPS server manages these crucial functions to maintain a secure and efficient network environment.
- User authentication: NPS authenticates users and devices attempting to connect to the network, ensuring that only those with valid credentials can gain access. This authentication process is crucial for securing network access points, such as VPNs, wireless networks, and dial-up connections.
- Authorization management: Once authenticated, NPS determines what resources the user or device is allowed to access based on predefined policies. This role is vital for enforcing security protocols and ensuring users can only reach areas of the network appropriate for their role and clearance.
Accounting and compliance
Accounting involves tracking and logging user activities and resource usage within the network, which is pivotal for auditing and monitoring purposes. The following list discusses how NPS aids in ensuring compliance with various regulatory standards, a critical factor for businesses in today’s data-sensitive world.
- Monitoring network usage: NPS tracks the activities of authenticated users on the network, logging details such as the duration of their connections, the services they use, and the data they transfer. This accounting feature is essential for auditing purposes, ensuring compliance with regulatory standards, and understanding network usage patterns.
- Compliance enforcement: By providing detailed records of network access and usage, NPS assists organizations in meeting various regulatory requirements, essential for businesses handling sensitive data.
Policy-based network management
Policy-based network management allows administrators to create and enforce specific network access policies, tailoring network security and usage according to organizational needs. Here is how NPS facilitates the creation of these policies and how they impact network security, user access, and overall network management:
- Network policies: NPS allows administrators to define and implement network policies that control access to network resources. These policies can be tailored to meet specific security needs and organizational protocols, providing a flexible yet secure network environment.
- Condition-based access control: NPS enables the creation of conditions for network access, such as time-of-day restrictions, group membership requirements, or the health of a device (in the context of Network Access Protection, or NAP).
Benefits of using NPS
The implementation of NPS in a network infrastructure offers a range of benefits that enhance both security and operational efficiency. These advantages make NPS a valuable asset for organizations looking to optimize their network management practices.
- Robust authentication and authorization: NPS strengthens network security by ensuring robust authentication and authorization of users and devices. This reduces the risk of unauthorized access and potential security breaches.
- Consistent policy enforcement: With NPS, network policies are applied uniformly across all access points. This consistent enforcement of security policies helps maintain a high-security standard throughout the network.
- Fine-grained access management: NPS enables administrators to define detailed access policies, granting appropriate access levels to different user groups. This granularity ensures that users have access only to the resources necessary for their roles.
- Dynamic response to security threats: NPS can be configured to respond to security incidents dynamically, such as temporarily increasing security measures during a detected threat.
- Adapts to organizational growth: NPS is scalable and can handle an increasing number of authentication requests as an organization grows. This scalability ensures that the network can expand without compromising on security or performance.
- Support for a variety of network types: NPS is versatile and supports various network types and access methods, including VPNs, wireless, and dial-up networks, making it a flexible solution for diverse network environments.
- Centralized management: By centralizing the management of network policies and access controls, NPS simplifies administrative tasks, saving time and reducing the likelihood of errors.
- Integration with existing systems: NPS integrates well with other Microsoft products and services, such as Active Directory, providing a seamless management experience.
- Detailed logging and reporting: NPS maintains comprehensive logs of network access and activities, which are invaluable for auditing purposes and to ensure regulatory compliance.
- Supports compliance requirements: The detailed accounting and reporting capabilities of NPS assist organizations in meeting various data privacy and security standards such as GDPR, HIPAA, and PCI DSS.
The 3 roles of NPS
NPS fulfills three key roles in managing network access and policies. Each role represents a distinct functionality that contributes to the comprehensive network management capabilities of NPS.
1. NPS as a RADIUS server
NPS processes authentication and authorization requests for network access. When a user or device attempts to connect to the network, NPS verifies their credentials and determines their access level based on predefined policies.
Additionally, NPS can work with a variety of network access servers, such as VPN servers, wireless access points, and dial-up servers, making it a versatile solution for different network types. It is also pivotal in enhancing network security by centralizing and streamlining the authentication process, thus efficiently managing user access across the network.
2. NPS as a RADIUS proxy
When functioning as a RADIUS proxy, NPS forwards authentication and configuration requests to other RADIUS servers in the network. This is particularly useful in complex or distributed network environments. Also, it can provide load balancing by distributing requests among multiple RADIUS servers and ensure continuity through failover mechanisms in case of server unavailability.
This role enables NPS to handle requests across different networks or sub-networks, facilitating seamless cross-network authentication and management.
3. NPS as a network policy server
NPS primarily manages and enforces network policies. It defines the conditions under which users and devices are granted or denied network access. It also allows the creation of policies based on various conditions like time of day, group membership, or the health status of a device, providing a high degree of control over network access.
In this role, NPS can also integrate with NAP to enforce device health policies, ensuring that only compliant and healthy devices can access or communicate on the network.
NPS best practices
Using NPS effectively requires adherence to certain network and server management best practices. These practices ensure that NPS operates efficiently, securely, and in alignment with the organization’s network management goals. Here are some recommendations from Microsoft:
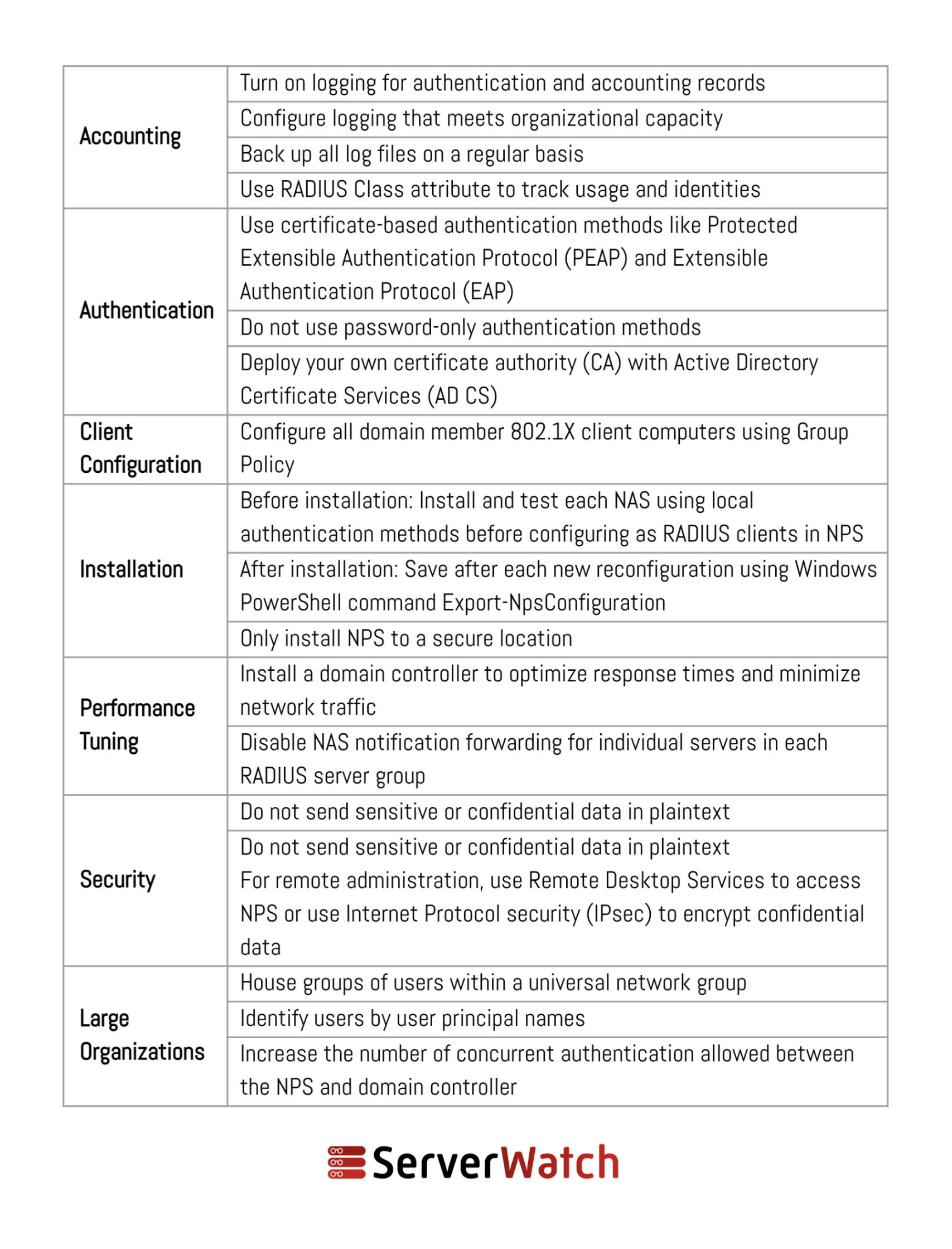
Below are some additional best practices to consider when deploying and managing an NPS.
- Regular policy review and update: Regularly review and update NPS policies to ensure they align with the latest organizational requirements and security standards. Modify policies in response to changes in network infrastructure or security landscape.
- Secure configuration and maintenance: Use strong authentication methods, like multi-factor authentication (MFA), to enhance security. Keep NPS and related network software up-to-date to protect against vulnerabilities and exploits.
- Scalable and redundant setup: Design the NPS deployment with scalability in mind to handle increasing loads and future network expansion. Implement redundancy and failover mechanisms to ensure NPS availability even during server or network outages.
- Efficient network policy design: Create clear, concise, and understandable policies to avoid confusion and ensure they are enforced as intended. Apply the principle of least privilege in policy design, granting users only the access necessary for their roles.
- Monitoring and auditing: Actively monitor NPS performance and access logs to quickly identify and respond to unusual activities or potential security breaches. Maintain comprehensive audit trails for compliance purposes and to analyze historical access and usage patterns.
- Integration with other systems: Integrate NPS with Active Directory for streamlined user authentication and management. Ensure compatibility and integration with other systems and services used within the network.
- User education and support: Educate users about network policies and the importance of adhering to security protocols. Provide clear support channels for users to report issues or seek assistance related to network access.
- Documenting procedures and policies: Maintain detailed documentation of NPS configurations, policies, and procedures for reference and training purposes. Document any changes made to the NPS setup or policies, including the rationale and impact of these changes.
Bottom line: The integral role of NPS in modern network management
NPS has emerged as an indispensable network and server tool offering a robust and flexible solution for ensuring secure and efficient network operations. The integration of NPS within an organization’s network infrastructure not only enhances security by enforcing rigorous access policies but also simplifies administrative tasks, leading to a more efficient management of network resources.
By adhering to best practices in deploying and managing NPS, organizations can significantly mitigate risks associated with network security and ensure a seamless operational flow.
Improve your NPS functionality and performance with one of the best free RADIUS server testing and monitoring tools, selected and reviewed by our experts.
Sam Ingalls contributed to this article.
Featured Partners: Network Monitoring Software
Paessler PRTG Network Monitor
Why Over 500,000 IT Pros Trust Paessler PRTG Network Monitor.
Paessler PRTG offers fast, easy setup and scalable monitoring for networks of all sizes. With auto-discovery, it quickly maps your network, monitoring bandwidth, devices, and traffic 24/7. Receive proactive alerts with customizable thresholds before issues impact users. Supporting SNMP, WMI, NetFlow, and more, PRTG improves network uptime and performance.
Try PRTG free for 30 days to experience its full capabilities with zero risk.
ManageEngine Log360
Log360 is a SIEM solution that helps combat threats on premises, in the cloud, or in a hybrid environment. It also helps organizations adhere to several compliance mandates. You can customize the solution to cater to your unique use cases. It offers real-time log collection, analysis, correlation, alerting and archiving abilities. You can monitor activities that occur in your Active Directory, network devices, employee workstations, file servers, Microsoft 365 and more. Try free for 30 days!
Site24x7
Site24x7 provides a comprehensive network monitoring tool to ensure the health and performance of your network devices and interfaces. Automatically discover your devices such as routers, switches, firewalls and continuously monitor critical metrics such as CPU, memory utilization, buffer hit stats, and more. This helps network admins monitor, visualize, optimize and manage the network devices and their respective interfaces.




