by Michael Bell
www.2000trainers.com
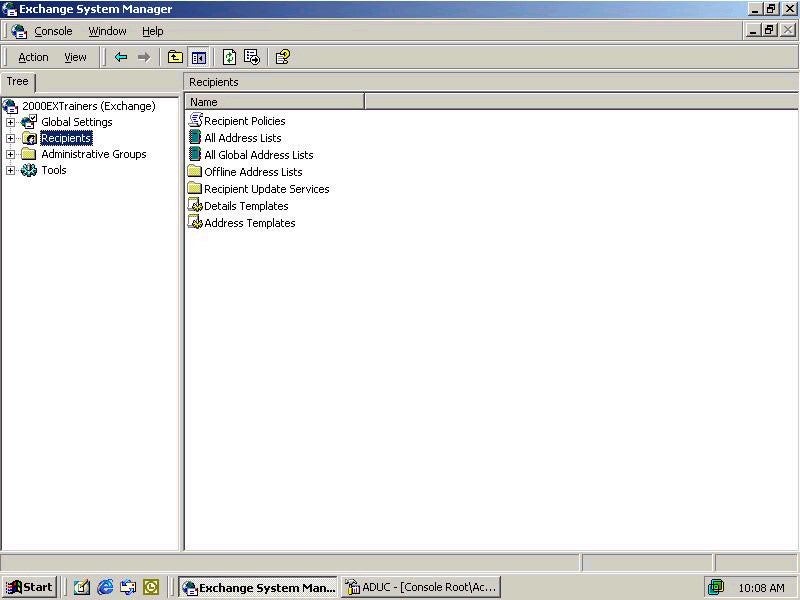
Ok, now that I have had a little bit of a break, I guess it is time to get back to the articles! Today we are going to talk about Recipient Policies. While not necessarily the most glamorous feature of Exchange 2000, Recipient Policies are definitely worth knowing about. In Exchange 5.5, similar functionality was found in the Site Addressing object. However, as you will see, Recipient Policies in Exchange 2000 are much more flexible than Site Addressing was in Exchange 5.5, as well as having additional functionality to boot. The first thing that we will look at will be where we go to create our Recipient Policy, which is the Exchange System Manager (ESM). Once we open up the ESM, we will see on the right hand side the Recipient Policy container, like so:
Michael Bell’s latest article in the Learning Exchange Server 2000 in 15 Minutes a Week series takes a look at Recipient Policies, Exchange 2000’s enhanced version of Exchange 5.5’s Side Addressing object.
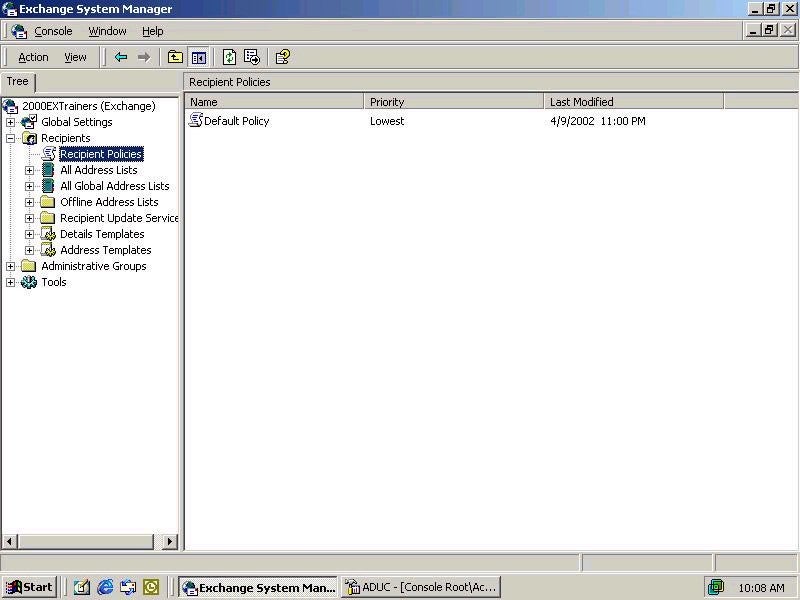
When we expand the Recipients container, the first thing listed under it should be our Recipient Policies, with the Default Policy listed over in the right hand pane as you can see here.
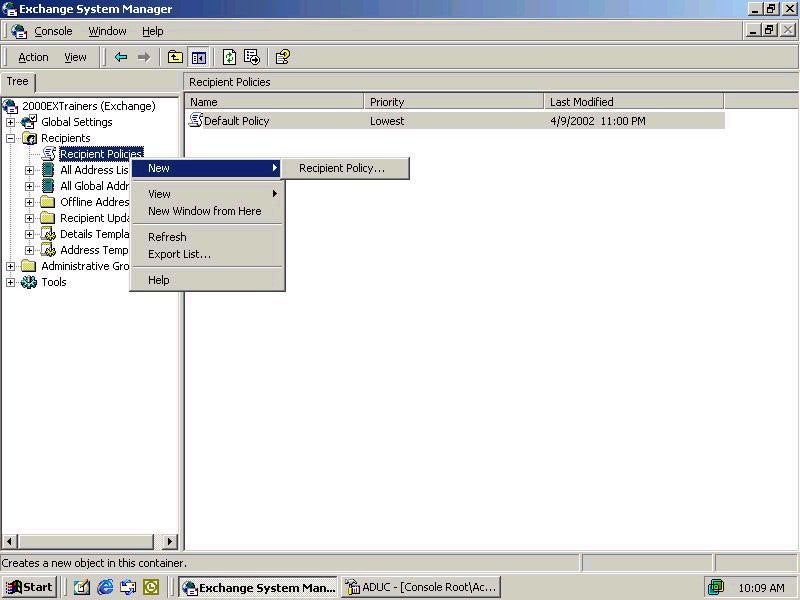
Now what we are going to do is take a look at how we create a new Recipient Policy. In my case I have decided that several of my users require an additional SMTP address so that they can continue to receive email from their old address as well as their new address. I right-click on the Recipient Policies container, and I should see something like this:
Now I can go ahead and configure my settings for this particular policy. As we can see, the first thing we must configure is a name for the new policy. Once we have specified that, we can actually get on with configuring the properties that will really matter as far as this policy is concerned. As I mentioned before, my goal was to create a secondary address that would be accessible by some of my users that have come over from a merger with another company. After defining a name for my policy, I select Modify from the General Tab, and this will allow me to create my LDAP filter that will be used to define what users, groups, or objects my new policy will effect. The screen should look like this:
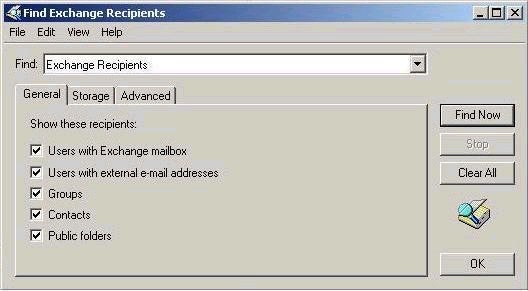
You should notice a couple of things about this particular utility. First off, it is the same utility that we can use to search through Active Directory to locate objects. Secondly, there are two parts to the search. First, we specify what type of object we want to find from the list box at the top of the dialog box, and then we select what type of recipients we want to filter, based on our earlier selection. You should notice that the available selections change, based on what you select from the Find drop down box. For example, if I wanted to filter based on Group Membership, I could create a filter similar to the following:
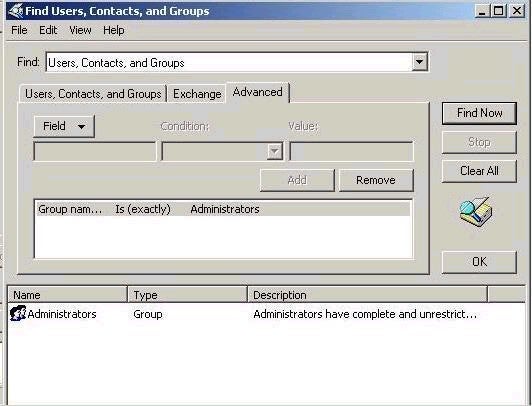
In this case, you should notice that I defined Users, Contacts and Groups as the focus of my search. I then went to the Advanced tab, and further stipulated that I only wanted to find a group called Administrators. In this way, I have complete flexibility and customizability when it comes to creating my Recipient Policies. In my case, though, I don’t want to filter based on Group Membership. Instead, I would like to filter my recipient addresses based on the defined value listed in the City field for the user object. To do so, I would define the following filter:
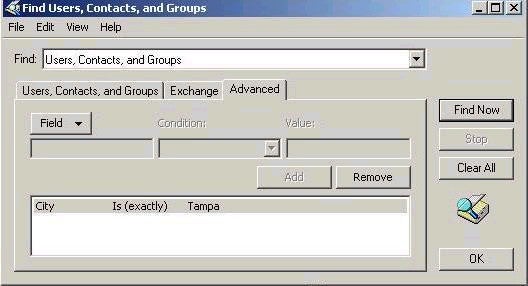
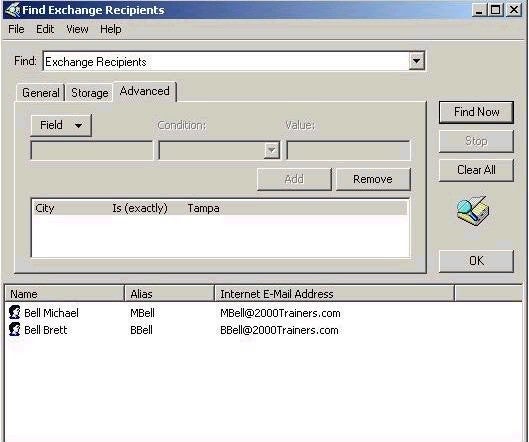
This should have the intended effect that I am looking for, in that it will allow me to define a secondary SMTP address that these users will be able to use in addition to the default address generated by the Default Recipient Policy. One thing that I can do to make certain that my new Recipient Policy is working correctly is to use the Find Now button from the filter dialog box to make certain that my LDAP filter is working properly. As you can see from the following graphic, my filter is working just fine.