

All this talk of configuration and
customization might have you a bit frightened. The good news is that by
default, the program has already grouped important security events into
categories based on their potential to represent threats. So, even if you’re
not sure what you want LANguard S.E.L.M. to tell you when starting out, the
default settings handle the most common requirements smoothly. For advanced
users, the ability to customize which events are monitored and how they are
characterized provides maximum flexibility. The screenshot below outline
the process of defining a custom event rule.
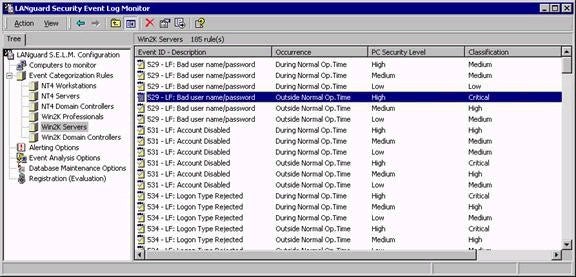
As far as event monitoring is concerned, the
LANguard S.E.L.M. Event Viewer makes things easy. While the standard Event
Viewer included with Windows 2000 adds all security alerts to a single log
file on each individual machine, LANguard S.E.L.M. Event Viewer instead
categorizes alerts according to how critical they are, as shown below.

Remember that even though the defaults work
well, you have the ability to define exactly how critical an event is
considered to be. For example, Event 529 (bad username/password) is
classified as a medium security event on a low security PC outside of Normal
Operation Time by default (as shown below). If you want, you can easily
change this setting to a high or even critical event – whatever best meets
the needs of your environment.
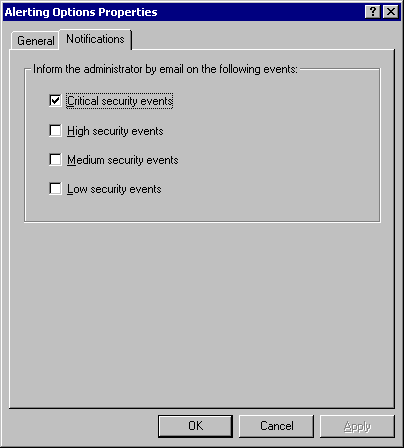
Taken a step further, you also control when
you are contacted by e-mail (this is configured for critical alerts only by
default). However, you can again define which types of events you wish to be
contacted about. Remember that receiving too many e-mail alerts may lead you
to start ignoring them, so be careful with the events that you decide to
define as critical or worthy of having an e-mail sent.
Property of TechnologyAdvice. © 2025 TechnologyAdvice. All Rights Reserved
Advertiser Disclosure: Some of the products that appear on this site are from companies from which TechnologyAdvice receives compensation. This compensation may impact how and where products appear on this site including, for example, the order in which they appear. TechnologyAdvice does not include all companies or all types of products available in the marketplace.