Standard Permissions
Once you have copied the permissions
locally (or removed them entirely), you can begin to set them
locally on the object. In order to set, add or change
locally copied permissions to any of the standard permission
levels, you need to open the Active Directory Users and
Computers MMC and find the object you want to administer.
Once you have done this, you need to right click the object to edit its
properties. You would go to the security tab and either add
or remove users in the upper portion of the security box to
allow and/or deny general access to the object.
[NOTES
FROM THE FIELD] – When you add a user or group, you
are preparing to explicitly set some level of access. When
you remove a current user or group or intentionally elect to
not add them, you are implicitly denying them access.
When permission to perform an
operation is not explicitly assigned, it is implicitly
denied. What this means is that if you are not given any
permissions to an object, you are denied access to it by the
fact that you have no access in the first place.
When permission to perform an
operation is implicitly assigned, it can be explicitly
denied. What this means is that if permissions are set via
inheritance or through group membership, it can be still set
to deny at a local object. If a specific user is gaining
access to an object through inheritance, you can set a local
deny for that user on the object itself. If a specific user
is gaining access to an object through group membership and
you want that group but not that given user to have
access, you can deny the user access locally at the object.
Once you have controlled which users or
groups that you want to allow (or deny) access to the object,
you can then set permission levels to them in the standard
permissions section in the lower part of the security tab.
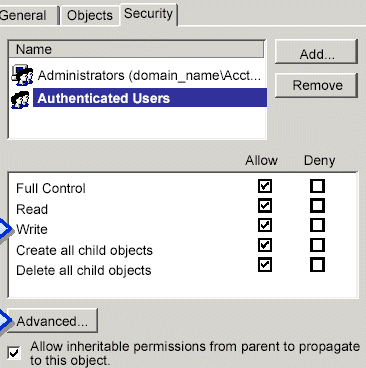
Full
Control allows you to change permissions and take ownership, as well as
perform the tasks that are allowed by all other standard
permissions.
Read allows
for the viewing of objects and object attributes, the object
owner, and the Active Directory permissions.
Write
allows for the ability to change the attributes of an object.
Create All Child Objects allows for the addition of any type of child
object in Active Directory.
Delete All Child Objects allows for the removal of any type of child
object in Active Directory.
While it is
possible to assign permissions directly to users, best
practices dictate that Administrators should only assign
permissions to groups for the easiest administration.

