by Dan DiNicolo
http://www.win2000trainer.com
Welcome to article number 14 in my 70-240 in 15 minutes a week series. This week’s article covers part 2 of Active Directory and DNS, completing the topics begun last week. This article covers the implementation aspects of Active Directory and DNS. This includes a look at the configuration of zones and zone properties in DNS, troubleshooting tools for DNS, as well as the installation of Active Directory domain controllers and related properties. Again, this topic ties into the Active Directory Implementation and Administration portion of the exam.
The material covered in this article includes:
– Service Records and locating domain controllers
– Configuring DNS zones properties
– DNS troubleshooting tools
– Installing Active Directory
– Troubleshooting the Active Directory Installation
Service Records and Locating Domain Controllers
Windows 2000 Active Directory requires DNS to function correctly. DNS support for SRV records is the only absolutely mandatory requirement for Active Directory to function. However, it is also recommended that your DNS server support dynamic updates, since domain controllers dynamically register a number of records in DNS. If your DNS servers do not support this, you would need to set up all required service records for all domain controllers manually, a potentially long and arduous process. Windows 2000 DNS supports both, as well as incremental zone updates
(IXFR). IXFR is useful in that it allows DNS servers to simply replicate zone changes instead of the entire zone file as in
AXFR-based implementations (NT 4 DNS, for example). It is also worth noting which versions of BIND (the popular Unix-based DNS server) support the above requirements:
BIND 4.9.7 – supports SRV records
BIND 8.2.1 – supports SRV records, Dynamic Update, IXFR
An understanding of the SRV records and related domains that you will find (or require) in a DNS implementation to support Active Directory is also important. Just to reiterate, Windows 2000 uses service records in DNS to locate domain controllers in specific domains, domain controllers in the same site, global catalog servers, key distribution centers, and more. A service record uses a standard record format, an example of which is shown below:
_service._protocol.name ttl class SRV priority weight port target
_Service represents the name of the service that a domain controller is running, such as ldap (for a domain controller), gc (for a global catalog server), kerberos for a key distribution center, and so forth.
_Protocol specifies the transport protocol used, such as TCP or
UDP.
Name specifies the domain name relating to the record, for example win2000trainer.com
Ttl specifies the time to live value, in seconds
Class specifies the DNS record class value, almost always ‘IN’ for Internet.
Priority specifies the priority level of the server. Clients will attempt to contact the server with the lowest priority value.
Weight is a load-balancing feature. If multiple servers have the same priority, clients choose SRV records with higher weights.
Port specifies the port number that a particular service listens on.
Target specifies the FQDN of the host running the service
As such, a domain controller with FQDN dc1.win2000trainer.com acting as a global catalog server would have a service record (as well as many others) as shown below:
_gc._tcp.win2000trainer.com 600 IN SRV 0 100 3268 dc1.win2000trainer.com
Domain controllers register their service records when their Netlogon service starts. As such, stopping and starting the domain controller’s Netlogon service can accomplish re-registration of all SRV records. You should also familiarize yourself with the different subdomains that are created beneath a domain in a Windows 2000 DNS implementation. The four main subdomains created are:
_msdcs – this subdomain is used to allow clients to find domain controllers providing specific services and running Windows 2000.
_sites – this subdomain is used to allow clients to find domain controllers providing specific services in a specific site.
_tcp – this subdomain lists services provided that use the TCP protocol to communicate.
_udp – this subdomain lists services provided that use the UDP protocol to communicate.
Service records and related entries can be verified by using both the DNS MMC snap-in, as well as by querying DNS using
nslookup.exe. The syntax to query a DNS server for a list of all service records for a given domain is shown below:
C:Nslookup
>ls -t SRV win2000trainer.com
Welcome to article number 14 in my 70-240 in 15 minutes a week series. This week’s article covers part 2 of Active Directory and DNS, completing the topics begun last week. This article covers the implementation aspects of Active Directory and DNS.
Configuring the DNS Server for Active Directory Support
Aside from the details listed above, it is important to understand how to create an initial DNS zone to support Active Directory. This should be done in advanced of installing Active Directory, in order to ensure that things are configured as you wish them to be. If you do not configure the zone in advance, the installation wizard will automatically do it for you, and the installation may not meet your needs.
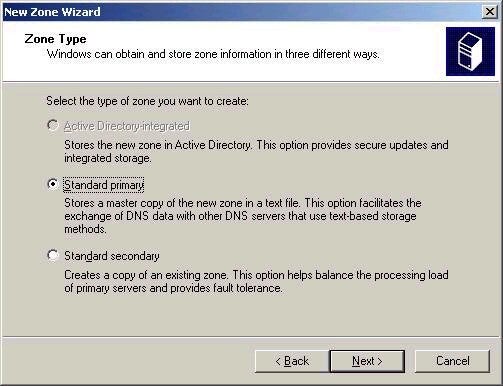
Configuring a zone first involves installing the DNS service via the Add/Remove Windows components wizard. After doing this, open the DNS tool and you should see a configuration as shown below:
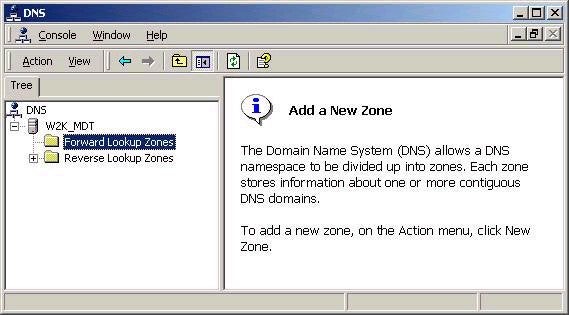
By default the server will act as a caching-only server, simply
forwarding queries to root servers when an answer cannot be
found in cache. However, in order to support AD, a zone must be
created that will be authoritative for the Active Directory
domain that is to be installed. A wizard does exist to walk you
through the process (right click and choose Configure the
Server) if you choose that method. However, right-clicking the
forward lookup zone and choosing New Zone will open the New Zone
wizard, which I will cover here. By default, three options exist
for zone types to be created, as shown below: